IT Risk Management is a security risk management technique used to mitigate IT risks, i.e., minimize the impact of software defects and security breaches on an organization’s data and technology systems. In simple terms, this refers to a continuous process for managing, planning, operating, and controlling the risks that can result from the application, system, or network of a computer-based organization.
In most organizations, IT Risk Management is an ongoing process, which means that there is continuous monitoring of the status of the organization’s IT systems and the ability to handle any given situation. This monitoring helps to identify risks early and reduce or eliminate them before they take place.
Understanding IT Risk Management
IT Risk Management starts with the assessment of risks. The first step is defining the objectives of IT Risk Management. These objectives are specified in terms of mission, business, and financial considerations and can include such things as customer satisfaction, revenue, and economic viability. Achieving these objectives involves identifying threats, vulnerabilities, and their effects. Identifying these requires both research and analysis of the organization, as well as the application in which they reside.
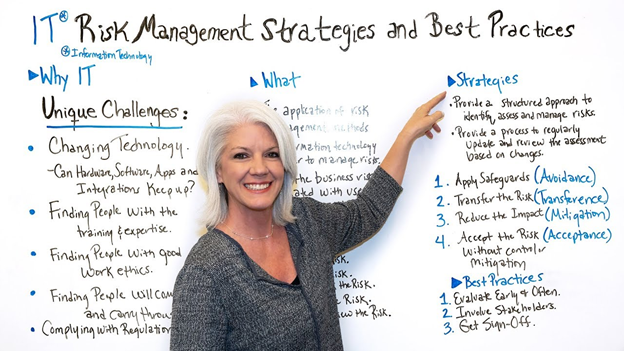
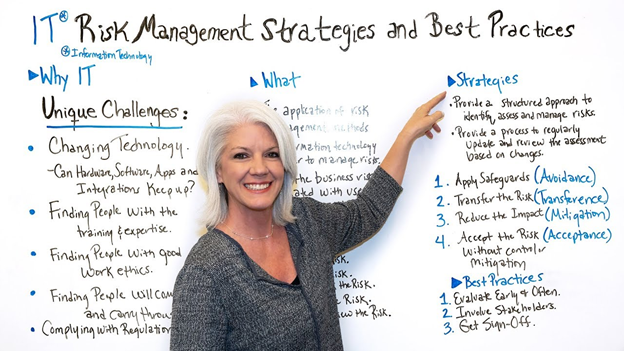
Why Is Having a Risk Management Strategy Important?
Once threats and vulnerabilities have been identified, organizations must develop a strategy for handling them. A successful IT risk strategy addresses both the short-term and long-term risks to an organization. One of the steps includes determining what actions should be taken in the face of an event. There are different strategies that an organization can follow. For instance, some organizations may choose to implement patch management programs, while others may choose to conduct vulnerability assessment programs.
A risk management strategy is typically implemented through a risk assessment template or a checklist. The assessment templates provide the basic information required for assessing risks and vulnerabilities. The tools used in performing an assessment include penetration testing, code review, and white-box testing. The techniques and tools that are used to perform these tests are based on industry standards. Once these tests are complete, the software can be deployed in a production environment.
Contingency Planning
Another approach to managing IT risks is through the implementation of a contingency plan. This contingency plan can include various types of risk assessment techniques. A key example of a contingency plan is a disaster recovery plan. The disaster recovery plan might include restoring critical information and data. In addition, it might also address issues such as restoring systems so that the users do not lose any critical data or restoring critical internet applications in case of a cyber attack.
IT Security Risk Assessment
IT Risk Management Strategies can be developed based on vulnerability assessment. When vulnerabilities are identified, they can be repaired. However, vulnerabilities cannot be identified without an assessment. Based on this assessment, these strategies can be developed. It could address issues such as preventing the access of a program or file by unauthorized users. It could also address issues such as maintaining network security, monitoring and controlling backup media, and firewalls.
Implementing Strategies
When assessing an issue, IT Risk Management Strategies can be implemented. One of the methods that can be used is to prioritize the risks. The topmost risk should be the one that needs to be addressed first. After this, secondary risks should be assessed according to their impact on the organization. The third risk should then be prioritized according to its impact on the organization.
IT Risk Management Strategies can help you prevent risks before they occur. They can also help you mitigate against their impact after they have occurred. This can be achieved by improving your knowledge of the risk and how it might arise. Organizations should therefore invest in a solid strategy—as it is an investment in your organization’s future.