SQL injection is one of the most persistent and damaging vulnerabilities in enterprise software, and COBOL-DB2 environments are not immune. Despite their reputation for reliability, many COBOL-DB2 systems were written decades ago with limited awareness of modern security practices. As a result, dynamic SQL construction, manual string concatenation, and outdated input handling techniques remain widespread, creating opportunities for attackers to exploit these systems.
Mainframes running COBOL-DB2 often support critical industries such as banking, insurance, and government services. They store and process sensitive customer data, financial transactions, and confidential records. A successful SQL injection attack can expose private data, enable unauthorized access, or disrupt essential business operations. These risks are magnified by the age and complexity of many codebases, where undocumented legacy logic and hard-coded shortcuts introduce additional vulnerabilities.
Addressing SQL injection in COBOL-DB2 requires a deep understanding of the language’s syntax, DB2’s embedded SQL features, and the typical patterns that can lead to unsafe code. Secure development practices such as using parameterized queries, validating and sanitizing input, and enforcing least-privilege database access help mitigate these risks. Effective detection also relies on thorough code review, specialized static analysis, and continuous monitoring to identify and remediate potential weaknesses before they can be exploited. By adopting these practices, development teams can strengthen the security posture of even the oldest and most mission-critical COBOL-DB2 applications.
Introduction to SQL Injection in COBOL-DB2
Mainframe applications are often seen as rock-solid, mature systems. Yet even these critical platforms can harbor significant security gaps, particularly when it comes to SQL injection vulnerabilities. COBOL-DB2 programs, which power essential business functions, frequently rely on dynamic SQL and manual input handling techniques that make them surprisingly vulnerable to injection attacks. Understanding why these programs are at risk is the first step toward effectively protecting them.
What Makes COBOL-DB2 Programs Vulnerable?
COBOL-DB2 programs often process vast amounts of business-critical data while using code written decades ago. Over the years, maintenance efforts have introduced shortcuts and workarounds that ignore modern security standards. One common source of vulnerability is dynamic SQL generation, where user input is directly concatenated into SQL strings without adequate sanitization. This approach increases flexibility but opens the door for injection attacks.
For example:
MOVE 'SELECT * FROM CUSTOMERS WHERE NAME = ''' TO SQL-STRING.
STRING USER-NAME DELIMITED BY SIZE INTO SQL-STRING.
In this code, user input is blindly appended to the SQL command. If an attacker supplies ' OR '1'='1, the resulting query returns all records. Combined with minimal input validation and inconsistent use of host variables, such patterns make these systems easy targets. Because COBOL-DB2 programs often run in trusted environments, developers may not expect malicious input, further increasing risk.
Risks of SQL Injection in Mainframe Environments
The potential impact of SQL injection on mainframes is particularly severe given their role in storing and processing sensitive data. Mainframes support critical sectors like finance, healthcare, and government, where a breach could expose millions of records, disrupt essential services, or compromise regulatory compliance. Attackers exploiting SQL injection vulnerabilities can execute unauthorized queries, retrieve sensitive information, or even modify or delete critical data.
Moreover, COBOL-DB2 applications often lack modern security layers found in newer systems. Security patches may be infrequent or difficult to apply, and tight integration with other legacy systems can spread risk. A single exploited vulnerability could provide lateral movement opportunities within an organization’s network. This makes SQL injection in mainframe contexts a high-value target for attackers who understand the aging, complex nature of these systems and their importance to business continuity.
Typical Attack Vectors in COBOL-DB2 (Dynamic SQL, User Input, Legacy Interfaces)
SQL injection attacks in COBOL-DB2 environments often exploit predictable patterns of dynamic SQL generation. Programs that use EXEC SQL statements with user-supplied data are particularly vulnerable if they lack strict input validation. For example, dynamic SQL in COBOL might use variables assembled from user input to construct queries at runtime:
EXEC SQL
PREPARE DYNAMIC-STMT FROM :SQL-STRING
END-EXEC.
EXEC SQL
EXECUTE DYNAMIC-STMT
END-EXEC.
Without proper sanitization, attackers can manipulate SQL-STRING to inject malicious commands. Legacy interfaces exacerbate the problem. Older batch jobs and terminal applications may lack modern input validation, allowing free-form text to reach critical SQL statements unchecked. Web services or middleware that bridge newer front-ends to COBOL-DB2 back-ends can introduce further risk if they fail to sanitize data before passing it to legacy code.
Such attack vectors exploit the trust that these systems often place in their inputs, assuming internal users or automated processes will behave correctly. Attackers leverage this assumption, feeding malicious strings through any available channel to execute unauthorized queries or tamper with data, making comprehensive input validation and secure coding practices essential for defense.
Business Impact of Successful SQL Injection Attacks
The consequences of a successful SQL injection attack on a COBOL-DB2 system can be catastrophic. Beyond immediate data breaches, attackers may gain unauthorized access to sensitive customer information, financial records, or personal identifiers. This can lead to regulatory violations, costly fines, and reputational damage that undermines customer trust.
In mission-critical environments, SQL injection can disrupt operations. An injected command might alter production data, disable critical processes, or interfere with billing and transaction systems. Recovery can be slow and expensive, especially if backups are compromised or if the attack remains undetected for long periods. For regulated industries, a breach often triggers mandatory disclosure requirements, exposing organizations to public scrutiny.
Mitigating these risks requires a multi-layered approach. Secure coding practices, thorough reviews of dynamic SQL usage, robust input validation, and continuous monitoring all play vital roles. Organizations cannot afford to ignore these threats, especially when mainframe systems remain integral to day-to-day operations. Recognizing the true impact of SQL injection is essential to prioritizing the security of COBOL-DB2 applications.
How SQL Injection Manifests in COBOL-DB2 Code
COBOL-DB2 systems often operate at the heart of critical business processes but can include design patterns that make them vulnerable to SQL injection attacks. Unlike modern languages with built-in libraries for parameterized queries, COBOL-DB2 development relies heavily on dynamic SQL and manual string manipulation. This reliance creates multiple pathways for attackers to inject malicious input and manipulate database queries. Understanding how these vulnerabilities arise is crucial for effectively securing legacy codebases.
Unsafe Concatenation of SQL Statements
One of the most common causes of SQL injection in COBOL-DB2 is the unsafe concatenation of user input into SQL statements. Developers often use string manipulation to construct queries dynamically, especially when dealing with flexible search criteria or report generation. However, this practice is inherently risky if user input is not thoroughly sanitized.
An attacker can exploit this by injecting malicious SQL code, altering the logic of the query. Because dynamic SQL in COBOL lacks automatic protections found in modern frameworks, this pattern is especially dangerous. Even in internal applications, assuming all users are trustworthy is a mistake that can have severe security consequences.
Safe coding practices replace such patterns with parameterized queries using host variables, eliminating the need to concatenate input directly. Reviewing and refactoring such code is essential to reduce exposure to SQL injection attacks.
Lack of Input Validation in EXEC SQL and CURSOR Use
Another vulnerability stems from failing to validate or sanitize user input before embedding it in EXEC SQL or CURSOR statements. COBOL-DB2 applications often rely on input from various channels, such as terminal sessions, batch files, or web front-ends. When these inputs are accepted without proper checks, they become vectors for SQL injection.
Consider:
EXEC SQL
DECLARE C1 CURSOR FOR
SELECT * FROM CUSTOMERS WHERE NAME = :USER-NAME
END-EXEC.
While host variables are safer than string concatenation, they can still be misused if user input isn’t validated. Attackers might supply unexpected characters designed to exploit weaknesses in parsing or back-end logic. Furthermore, older COBOL programs may use dynamic SQL with prepared statements that simply concatenate user input without any parameter binding.
Comprehensive input validation, such as enforcing data type constraints, whitelisting acceptable values, and sanitizing special characters, is critical. Even when using host variables, developers must treat all user input as untrusted and apply validation rigorously to prevent injection attacks.
Examples of Vulnerable COBOL-DB2 Coding Patterns
Recognizing risky coding patterns is essential for any detection or remediation effort. Legacy COBOL-DB2 programs often include numerous examples of poor practices that attackers can exploit. Common patterns include direct user input in WHERE clauses, unescaped dynamic SQL strings, and insufficient checks on concatenated commands.
Example of unsafe dynamic SQL:
STRING 'DELETE FROM ORDERS WHERE ID = ' DELIMITED BY SIZE
USER-INPUT-ID DELIMITED BY SIZE
INTO SQL-STRING
Such patterns create direct injection points when user-supplied values are not properly validated or sanitized. Attackers can craft inputs that modify or extend SQL commands, potentially executing arbitrary queries, deleting data, or exposing sensitive information.
Identifying these patterns during code reviews and static analysis is vital. Teams should prioritize refactoring to use parameterized queries and host variables correctly. In some cases, breaking complex procedures into smaller, more focused routines can simplify validation and reduce the overall risk surface.
Challenges with Legacy Code and Maintenance
Securing COBOL-DB2 applications is particularly challenging because of their age and complexity. Many mainframe systems have evolved over decades, accumulating layers of business logic, undocumented features, and technical debt. Teams maintaining these systems may lack the institutional knowledge needed to understand why certain design choices were made or how different modules interact.
Legacy code often resists change. Refactoring large, intertwined routines can be risky, potentially introducing new bugs or breaking business-critical functionality. Additionally, older systems may use outdated development tools or lack modern testing frameworks, making comprehensive validation harder to achieve.
These challenges make proactive security reviews and continuous monitoring essential. Organizations should prioritize the most exposed and frequently modified components for initial remediation. Incremental improvements, combined with strong testing practices, can help reduce complexity and improve security over time. Recognizing these limitations is key to developing a realistic, sustainable strategy for securing COBOL-DB2 systems against SQL injection and other threats.
Techniques for Detecting SQL Injection Manually
Finding SQL injection vulnerabilities in COBOL-DB2 systems often begins with manual analysis. While automated tools can streamline detection, understanding the fundamentals of how to spot high-risk code patterns remains essential. Manual techniques allow developers and security analysts to apply contextual understanding to legacy systems where documentation may be sparse and design decisions opaque. These methods form the first line of defense, helping teams identify vulnerable areas before attacks can exploit them.
Manual Code Reviews: Spotting High-Risk SQL Statements
Manual code reviews are one of the most effective ways to identify SQL injection risks in COBOL-DB2 applications. Reviewers examine program logic, focusing on how SQL statements are constructed and where user input is introduced. Particular attention is paid to dynamic SQL, where input may be concatenated into commands.
While host variables provide some protection, input validation must be confirmed. Effective code reviews look for consistent patterns of sanitization, proper use of parameterized queries, and avoidance of unsafe concatenation. They also check for repeated logic that can be refactored, making input handling safer and easier to maintain. By systematically reviewing these areas, teams can highlight high-risk statements that need remediation.
Tracing Dynamic SQL Generation in COBOL Code
Dynamic SQL is common in COBOL-DB2 systems because it offers flexibility in building queries at runtime. However, this same flexibility makes tracing injection risks more complicated. Manual analysis requires understanding how variables flow through the code and where user input might influence SQL commands.
Manual tracing involves following variables from input to execution, looking for any gaps in validation or sanitization. This process often uncovers subtle issues, such as input accepted from batch files or older interfaces that were assumed to be secure. By carefully following these paths, security teams can detect injection opportunities that automated tools might miss or struggle to interpret in highly customized legacy systems.
Testing with Crafted Input (Error-Based and Behavioral Detection)
Beyond reading code, manual testing with crafted inputs is a practical method to confirm the presence of SQL injection vulnerabilities. Security testers supply malicious or unexpected inputs through all available channels, observing how the system responds. This approach is especially effective for uncovering error-based injection, where improperly handled input causes the database to return error messages revealing the underlying SQL.
For example, providing input like:
' OR '1'='1
can expose flaws if the system returns all records or throws an error that reveals the query structure. Behavioral detection involves watching for changes in application behavior, such as altered result sets or unauthorized access, when malicious input is used.
Manual testing is particularly important for COBOL-DB2 systems with multiple interfaces. Batch jobs, screen applications, and API endpoints can all serve as entry points for injection if they pass user-supplied data to SQL without validation. By systematically testing these paths, teams can discover vulnerabilities that might remain hidden in code reviews alone, ensuring a more thorough assessment.
Documenting and Prioritizing Findings for Remediation
Detection is only the first step; effective remediation relies on clear documentation and prioritization of vulnerabilities. Teams should record each finding with details about the vulnerable code, the nature of the risk, and recommended mitigation strategies. Documentation helps ensure that remediation is systematic and comprehensive rather than piecemeal.
For instance, a record might include:
- Location: Program XYZ, Line 150
- Issue: Dynamic SQL concatenating unvalidated USER-NAME
- Risk: SQL Injection leading to unauthorized data access
- Recommendation: Replace with parameterized query using host variables and input validation
Prioritization is equally important. Not all vulnerabilities carry the same risk, so teams should focus first on code that handles sensitive data or is frequently executed. Legacy systems often have limited resources for maintenance, making it essential to tackle the highest-risk issues first.
By maintaining clear, actionable records of SQL injection risks, organizations can plan remediation projects more effectively, coordinate across teams, and ensure that critical vulnerabilities are addressed without disrupting essential operations. This approach turns detection efforts into lasting security improvements.
Best Practices for Prevention in COBOL-DB2
Securing COBOL-DB2 applications against SQL injection attacks requires more than patching individual issues. It demands adopting strong, consistent development practices that prevent vulnerabilities from arising in the first place. While legacy systems introduce special challenges, developers can still apply proven techniques to improve security and reduce risk across the entire codebase. By enforcing these best practices, teams build resilience into their applications, making them far less attractive targets for attackers.
Using Parameterized Queries and Host Variables
One of the most effective strategies for preventing SQL injection in COBOL-DB2 is the use of parameterized queries with host variables. Unlike dynamic SQL assembled through concatenation, parameterized statements separate the SQL command structure from the data values. DB2 prepares these statements in advance, ensuring that user input cannot alter the intended command.
A safe pattern looks like this:
EXEC SQL
SELECT * FROM CUSTOMERS WHERE NAME = :USER-NAME
END-EXEC.
Here, :USER-NAME is a host variable bound securely at execution time. This approach eliminates the need for string concatenation that attackers can exploit. Even if a user provides malicious input, it is treated as a literal value rather than executable code. Teams maintaining COBOL-DB2 systems should systematically replace dynamic SQL with host-variable patterns wherever possible. Training developers on this practice is equally important to ensure it becomes standard operating procedure.
Input Validation and Whitelisting Strategies
Parameterized queries alone are not enough. Input validation is essential to ensure that only expected, safe values enter the system. COBOL-DB2 applications often interact with a range of input sources, from online forms to batch processes. Each of these entry points can become an injection vector if data is not validated properly.
Effective validation means defining strict rules for what constitutes acceptable input. For example, if a field should contain only alphabetic characters, reject anything else. Whitelisting explicitly specifying allowed values is far safer than blacklisting known bad patterns, which attackers can often bypass.
Example validation in COBOL might look like:
IF USER-NAME NOT ALPHABETIC
MOVE 'INVALID INPUT' TO ERROR-MSG
GO TO ERROR-HANDLER
END-IF.
By enforcing strict checks on all user input, developers can prevent harmful data from ever reaching SQL execution stages. This approach significantly reduces the risk of SQL injection while improving overall data quality and system reliability.
Minimizing Dynamic SQL Use When Possible
While dynamic SQL offers flexibility, it introduces significant risk if not used carefully. In many COBOL-DB2 applications, dynamic SQL is overused even when static or parameterized statements would suffice. Reducing dependence on dynamic SQL is a powerful strategy for minimizing injection risk.
Teams should audit their code to identify places where dynamic SQL is unnecessary. For example, queries with a fixed structure and predictable parameters can almost always be rewritten using static SQL with host variables. Even when dynamic SQL is unavoidable such as for flexible reporting requirements—it should be designed carefully, with rigorous input validation and use of prepared statements.
Minimizing dynamic SQL not only reduces the attack surface but also simplifies maintenance. Static queries are easier to read, test, and verify for correctness, making them preferable in most cases.
Implementing Least-Privilege Access Control in DB2
Even with perfect input validation and safe query construction, database access controls provide a critical last line of defense. The principle of least privilege ensures that each user or application component can access only the data and operations necessary for its role.
For DB2 systems, this means defining precise permissions for each program, user, or service account. Avoid granting broad privileges like DBADM or ALL PRIVILEGES unless absolutely necessary. Instead, limit access to specific tables, views, or stored procedures required for the application’s functions.
For example:
GRANT SELECT ON CUSTOMERS TO APP-USER;
This approach limits the potential damage even if an injection attempt succeeds. An attacker exploiting a vulnerability would only have access to the minimal data or operations allowed to that account. Regularly auditing database permissions helps ensure that privilege creep does not undermine these safeguards over time.
By enforcing least-privilege principles alongside other secure coding practices, organizations create layered defenses that make SQL injection attacks far less likely to succeed.
Automating Detection and Remediation with SMART TS XL
Manual techniques and best practices are essential for preventing SQL injection, but they are often not enough for managing large, complex COBOL-DB2 codebases. Legacy systems can contain thousands of lines of code developed over decades by different teams. Identifying all injection risks manually is time-consuming and error-prone. Automation fills this gap by systematically scanning for vulnerabilities, tracking changes over time, and guiding remediation efforts. SMART TS XL is purpose-built to help teams manage these challenges in COBOL-DB2 environments, offering advanced static analysis capabilities tailored to the unique requirements of mainframe applications.
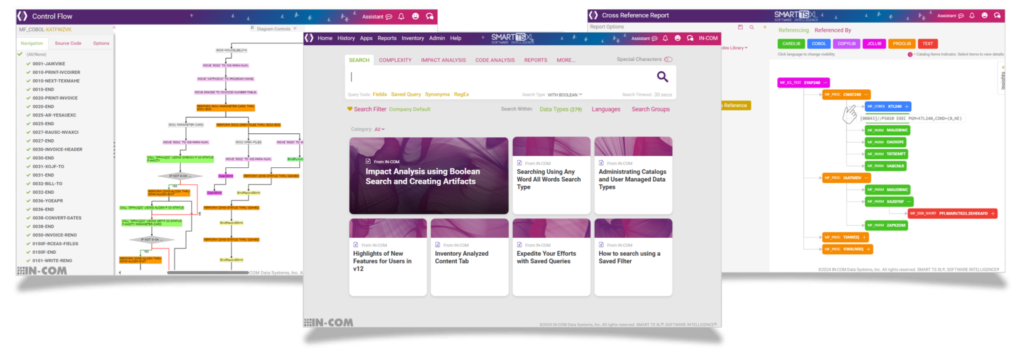
How SMART TS XL Scans for SQL Injection Vulnerabilities in COBOL-DB2
SMART TS XL performs deep static code analysis to identify SQL injection risks in COBOL-DB2 programs. Unlike generic scanning tools, it understands the syntax and structure of COBOL code, including embedded DB2 SQL statements. By parsing the code at a granular level, SMART TS XL can identify dynamic SQL construction patterns, improper use of string concatenation, and unsafe variable bindings that might lead to injection vulnerabilities.
It can also detect unsafe usage of prepared statements without parameter binding, alerting developers to potential injection vectors. This level of precision is critical in mainframe environments where SQL is often deeply intertwined with business logic and can be challenging to review manually. By scanning entire codebases systematically, SMART TS XL ensures that no hidden injection risks are overlooked.
Key Features for COBOL-DB2 Analysis (Pattern Recognition, Data Flow Tracking)
One of SMART TS XL’s most powerful capabilities is its ability to recognize high-risk coding patterns specific to COBOL-DB2. The tool includes a rich library of known insecure patterns and customizable rules that reflect real-world mainframe development practices. It identifies issues such as concatenated SQL strings, unsanitized user input, and inconsistent use of host variables.
Beyond pattern matching, SMART TS XL performs sophisticated data flow analysis. This means it can trace how user input moves through the code, even across different programs or modules, to determine whether it might reach a SQL execution point unsanitized. For example, it can detect if a variable populated from a user interface is later used in an EXEC SQL block without validation:
EXEC SQL
PREPARE DYN-STMT FROM :SQL-COMMAND
END-EXEC.
By analyzing these data flows, the tool helps teams understand not just where vulnerabilities exist but how they can be exploited, offering a far more comprehensive view of application security.
Guided Remediation with SMART TS XL
Identifying vulnerabilities is only half the battle; fixing them effectively is just as important. SMART TS XL goes beyond detection by providing actionable remediation guidance tailored to COBOL-DB2 code. When a vulnerability is flagged, the tool explains why it is risky, shows the exact code location, and suggests specific changes to eliminate the problem.
For example, SMART TS XL might recommend replacing unsafe string concatenation with a parameterized EXEC SQL block using host variables. It also highlights places where input validation should be strengthened or dynamic SQL usage minimized. By offering this targeted guidance, SMART TS XL reduces the learning curve for developers who may not be security experts but are responsible for maintaining critical legacy systems.
This support for guided remediation ensures that fixes are consistent, effective, and aligned with best practices, reducing the likelihood of reintroducing vulnerabilities in future updates.
Generating Reports for Compliance and Auditing
Security is not just about fixing code; it also requires demonstrating to stakeholders that systems are being properly maintained and monitored. SMART TS XL includes robust reporting features that help teams document their efforts to reduce SQL injection risks.
These reports can include:
- Lists of identified vulnerabilities, with severity ratings
- Locations of risky code patterns
- Status of remediation efforts
- Historical trends showing reduced risk over time
Such documentation is invaluable for internal reviews, external audits, and regulatory compliance requirements. By providing clear, actionable evidence of security improvements, SMART TS XL helps organizations maintain trust with customers, regulators, and executive leadership.
Automating these reporting tasks also reduces the manual burden on development teams, freeing them to focus on delivering secure, reliable software. In this way, SMART TS XL supports not only technical remediation but also the broader governance and compliance processes that are essential for modern mainframe security.
Case Study: Remediating a SQL Injection Vulnerability
Real-world examples are invaluable for understanding how SQL injection issues manifest in COBOL-DB2 applications and how they can be effectively remediated. Many legacy systems in critical industries contain vulnerable code written long before security best practices were widely adopted. By examining how an actual vulnerability is discovered, analyzed, and fixed, teams can better appreciate the value of systematic detection and the importance of modern tools and practices.
Identifying a Real SQL Injection Flaw in Legacy COBOL-DB2 Code
Consider a COBOL-DB2 program developed to support a customer service application. The code includes a feature for searching customer records based on user input received through a terminal interface. Originally built to be flexible, it uses dynamic SQL generated from concatenated strings:
MOVE 'SELECT * FROM CUSTOMER WHERE NAME = ''' TO SQL-CMD.
STRING USER-NAME DELIMITED BY SIZE INTO SQL-CMD.
During routine review, this pattern raises immediate red flags. Because the user input is directly inserted into the SQL command without sanitization or parameterization, an attacker can craft input like:
' OR '1'='1
This input alters the WHERE clause, causing the query to return all records. Such a flaw can lead to unauthorized access to sensitive customer information and violates data protection requirements. Recognizing this vulnerability early is critical to preventing exploitation, especially since the code may have run unnoticed for years without scrutiny.
Applying Automated Analysis to Pinpoint the Issue
Detecting the vulnerability manually is possible but time-consuming, particularly in large codebases. Using SMART TS XL streamlines this process. The tool scans the entire COBOL-DB2 application and identifies SQL command construction involving direct string concatenation with user input.
It flags the problematic lines, offering detailed explanations:
Potential SQL Injection Risk: Dynamic SQL constructed via concatenation.
Location: Program CUSTOMER-SEARCH, Line 145.
Beyond highlighting the specific line of code, SMART TS XL performs data flow tracking, confirming that USER-NAME is sourced from terminal input without any validation or sanitization steps. This precision allows teams to focus their remediation efforts exactly where needed, saving significant time and reducing the chance of overlooking similar issues in other parts of the application.
Steps Taken to Refactor and Harden the Code
Once identified, the remediation plan involves replacing unsafe dynamic SQL with a secure, parameterized approach using host variables. The refactored code might look like this:
EXEC SQL
SELECT * FROM CUSTOMER WHERE NAME = :USER-NAME
END-EXEC.
Before implementing this change, the team also enhances input validation to ensure only alphabetic characters are accepted:
IF USER-NAME NOT ALPHABETIC
MOVE 'INVALID INPUT' TO ERROR-MSG
GO TO ERROR-HANDLER
END-IF.
These modifications eliminate the injection vector by preventing malicious input from altering SQL command structure. Extensive testing follows, validating that the application continues to function correctly while resisting attempts to inject malicious SQL. Documentation of the change ensures that future developers understand why the refactoring was performed and how it strengthens security.
Post-Remediation Outcomes: Performance and Security Gains
After remediation, the team observes clear benefits. Security risk is greatly reduced because user input can no longer change the SQL logic. Sensitive customer data is protected, helping the organization maintain regulatory compliance and avoid costly breaches. Automated scans confirm the issue is resolved and highlight the overall reduction in high-risk patterns across the codebase.
Performance also improves subtly. Removing dynamic SQL construction reduces the overhead of preparing and parsing variable SQL strings at runtime. Instead, DB2 can optimize static, parameterized queries more effectively. The team gains confidence in their code quality and can demonstrate these improvements through detailed reports generated by SMART TS XL, supporting both internal security governance and external compliance requirements.
By taking a structured approach to detection, remediation, and verification, organizations can transform even the most dated COBOL-DB2 applications into secure, maintainable, and reliable systems ready to support modern business demands.
Strategies for Ongoing Security
Securing COBOL-DB2 applications against SQL injection is not a one-time task but a continuous commitment. Legacy systems often evolve slowly, but new features, maintenance updates, and changing user requirements can reintroduce risk over time. Sustainable security depends on embedding best practices into the software development lifecycle, using automated tools for monitoring, and cultivating a security-minded culture across development teams. By adopting proactive strategies, organizations can ensure that their critical mainframe applications remain resilient in the face of evolving threats.
Integrating Static Analysis into CI/CD for Mainframe Projects
Modern development teams increasingly use Continuous Integration and Continuous Delivery (CI/CD) pipelines to automate builds, tests, and deployments. For COBOL-DB2 projects, integrating static code analysis into these pipelines offers a robust defense against SQL injection. Static analysis tools can automatically scan new or modified code for risky patterns, enforcing security standards before changes are deployed to production.
A typical CI/CD workflow might include a step that runs static analysis after code commits:
step:
name: Static Code Analysis
command: run-analysis --target=COBOL
If the analysis identifies SQL injection risks, the pipeline can halt, preventing unsafe code from advancing. This approach enforces security consistently across the team, regardless of individual developer experience. It also reduces the cost of fixing vulnerabilities by catching them early, making secure development an integral part of daily workflows rather than an afterthought.
Scheduling Regular Security Scans of Legacy Code
Even without frequent changes, legacy COBOL-DB2 systems should undergo regular security reviews. Static analysis tools should be configured to perform comprehensive scans of the entire codebase on a scheduled basis weekly, monthly, or quarterly, depending on business needs. These scans can identify new risks introduced by system updates, configuration changes, or evolving threat models.
Regular scans provide historical insight into security posture over time. Teams can track metrics such as the number of SQL injection risks detected and remediated, demonstrating continuous improvement to auditors, management, and regulators. By maintaining this discipline, organizations ensure that even the oldest and most stable systems do not become blind spots for security.
Scheduled scans also support knowledge sharing. Developers can review reports to learn about common coding errors, reinforcing secure practices and building a culture where security is a shared responsibility rather than a specialized task for a few experts.
Training Development Teams to Recognize and Mitigate Injection Risks
Technology alone cannot secure software without knowledgeable people using it effectively. Investing in training is critical to help COBOL-DB2 developers understand how SQL injection attacks work, why legacy patterns can be dangerous, and how to implement secure alternatives. This is especially important in mainframe environments where teams may include developers with decades of experience but limited exposure to modern security practices.
Training sessions can cover topics such as:
- Identifying unsafe dynamic SQL patterns
- Implementing parameterized queries with host variables
- Validating and sanitizing input effectively
- Understanding least-privilege principles in DB2 authorization
Workshops, code review sessions, and even short documentation guides can improve security awareness across the team. When developers are equipped to recognize risks early, they make better design decisions and contribute to a more secure codebase over time.
Maintaining Secure Coding Standards Across Teams
As COBOL-DB2 projects often involve multiple teams and long-lived codebases, maintaining consistent security standards is essential. Organizations should establish clear guidelines for secure SQL usage, input validation, dynamic SQL management, and database privilege configuration. These standards should be documented, regularly reviewed, and updated to reflect evolving threats and best practices.
Enforcing these standards requires collaboration between development, security, and operations teams. Regular code reviews, automated static analysis in CI/CD pipelines, and shared knowledge repositories all help maintain alignment. By standardizing secure coding practices, organizations reduce the chance of vulnerabilities slipping through due to inconsistent approaches or knowledge gaps between teams.
Maintaining these strategies over time helps ensure that even the most complex and mission-critical COBOL-DB2 systems can resist SQL injection attacks and continue to support business goals securely and reliably.
Why SQL Injection Remains a Persistent Threat on Mainframes
Securing COBOL-DB2 applications against SQL injection is an essential responsibility for organizations that depend on mainframe systems to run critical operations. These environments often support vital business functions in banking, insurance, government, and healthcare. Yet their age and complexity mean that many contain code written before modern security best practices were well understood. Dynamic SQL generation, manual string concatenation, and insufficient input validation are common, creating significant opportunities for attackers to compromise sensitive data and disrupt services.
SQL injection remains a persistent threat because it exploits the way applications construct and execute SQL commands. Even small oversights in input handling can open the door to devastating breaches. Unlike newer platforms with built-in protections, COBOL-DB2 systems often rely on developers to enforce security manually. Addressing these risks requires a combination of secure coding practices, rigorous input validation, least-privilege database configurations, and regular code reviews. By making these measures part of the development culture, organizations can reduce vulnerabilities at the source.
Automated static analysis adds an essential layer of defense to these efforts. Tools like SMART TS XL enable development teams to systematically scan large, complex COBOL-DB2 codebases for SQL injection risks, identify unsafe coding patterns, and track data flow to detect vulnerabilities that manual reviews may miss. By integrating automated analysis into CI/CD pipelines and routine maintenance workflows, organizations ensure that new risks are detected and addressed before they can be exploited. Detailed reporting and guided remediation features help teams understand exactly where vulnerabilities exist and how to fix them effectively.
Ongoing security is not just about fixing today’s issues but also about building processes and habits that prevent tomorrow’s. Organizations should prioritize regular scans, consistent coding standards, and developer training to maintain strong security postures over time. By combining disciplined manual practices with advanced automated analysis, even the most complex and legacy-heavy COBOL-DB2 environments can be made resilient against SQL injection attacks, protecting critical data, maintaining compliance, and preserving customer trust for years to come.


