Rust has rapidly emerged as a go-to systems programming language, praised for its robust safety guarantees, expressive type system, and zero-cost abstractions. Yet despite its reputation for preventing entire classes of runtime errors through its borrow checker and strict compile-time checks, writing production-grade Rust still demands rigorous attention to quality, maintainability, and security.
As projects grow in scale and complexity, even the most disciplined teams can introduce subtle bugs, style inconsistencies, or security vulnerabilities. This is where static code analysis proves indispensable. By inspecting source code without executing it, these tools can uncover potential errors early, enforce coding standards across teams, and ensure compliance with security best practices.
For Rust developers, static analysis is more than a safety net. It complements the compiler’s strictness by adding targeted linting, security scanning, and advanced diagnostics tailored to evolving project needs. In this article, we will explore some of the most effective static analysis tools available for Rust today. From community-driven linters to sophisticated vulnerability scanners, these solutions empower development teams to maintain high standards of code quality, reduce technical debt, and deliver reliable software in an increasingly demanding landscape.
SMART TS XL
Maintaining quality in modern Rust development is challenging, even with the language’s strong safety guarantees. SMART TS XL is designed to help teams build reliable, maintainable, and secure software by offering deep static analysis capabilities tailored to Rust’s unique features. It supports professional engineering workflows by catching issues early, enforcing consistency, and reducing manual review effort.
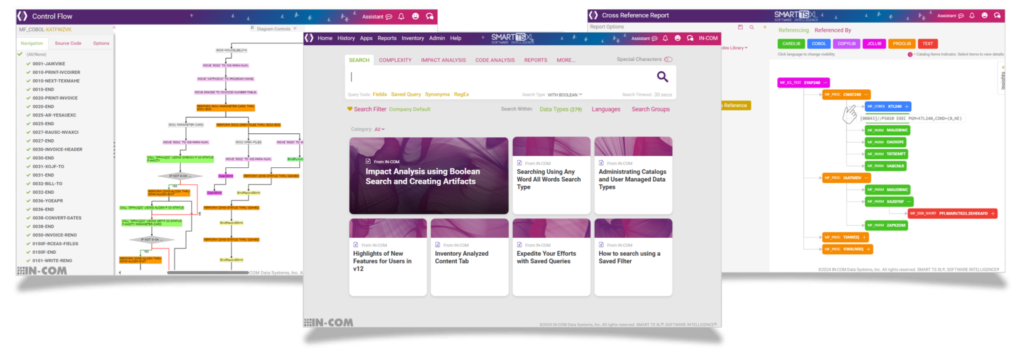
SMART TS XL stands out with a range of features that make it an excellent choice for teams working on Rust projects:
- In-depth semantic analysis
Goes beyond simple linting by understanding the relationships between functions, modules, and ownership patterns. Identifies subtle issues such as concurrency risks, improper borrowing, lifetime mismanagement, and logical errors that can be difficult to spot during code review. - Advanced linting and style enforcement
Enforces coding guidelines automatically to maintain a consistent codebase. Teams can define custom lint rules to match internal standards or adapt industry best practices, ensuring code remains readable and maintainable over time. - Security vulnerability detection
Analyzes code for insecure patterns, unsafe blocks, and common vulnerabilities. Includes scanning for known issues in dependencies, helping developers maintain a strong security posture and reduce exposure to supply chain risks. - Configurable rule sets
Offers flexibility to tailor analysis to the needs of different projects or teams. Rules can be customized, enabled, or disabled as required, ensuring that analysis is both relevant and actionable without generating noise. - Scalable analysis for large codebases
Optimized to handle projects ranging from small open-source libraries to complex, enterprise-grade systems with extensive module hierarchies. Maintains fast analysis times without sacrificing depth or accuracy. - Comprehensive reporting
Produces detailed, easy-to-read reports highlighting issues by severity, location, and recommended fix. Supports integration into documentation systems or ticketing workflows to track and manage technical debt over time. - CI/CD integration
Designed to fit into modern DevOps pipelines. SMART TS XL can be integrated into continuous integration systems to block deployments with critical issues, enforce quality gates, and maintain high standards throughout the development lifecycle. - Collaboration support
Helps teams align on quality expectations by providing consistent, automated feedback on every change. Reduces friction in code reviews by offloading routine checks to the analysis tool, freeing engineers to focus on design and architecture discussions. - IDE integration and developer experience
Offers integration options with popular editors and IDEs so developers receive real-time feedback as they write code. Helps catch issues at the earliest stage of development, reducing costly fixes later. - Cross-language and multi-project analysis
Supports projects that include multiple languages or interoperate with other systems. This flexibility is essential for Rust teams working in polyglot environments where Rust modules interact with other stacks.
By providing this level of comprehensive, configurable analysis, SMART TS XL serves as more than just a linting tool. It acts as a powerful safeguard for code quality and security in professional Rust development. Teams that adopt SMART TS XL can expect fewer bugs in production, faster code reviews, reduced technical debt, and stronger confidence in the long-term maintainability of their codebase.
Clippy
Clippy is the Rust community’s standard static analysis tool, integrated directly with the official Rust toolchain and widely used by developers to improve code quality and enforce idiomatic practices. It serves as a valuable first layer of automated code review, offering comprehensive linting that aligns with the language’s philosophy of safety and expressiveness. Developers can run it easily with the cargo clippy command, making it highly accessible and well-suited to projects of any size.
Key features include:
- Extensive lint catalog
Offers hundreds of built-in lints across categories such as correctness, performance, style, and complexity. These lints help catch common mistakes and guide developers toward idiomatic Rust usage. - Idiomatic enforcement
Encourages best practices by flagging non-idiomatic patterns and suggesting safer, more efficient Rust constructs. This helps teams maintain consistency and improves long-term maintainability. - Seamless cargo integration
Runs as part of the standard Rust development workflow without needing additional installation. Configurable throughclippy.tomlto enable or disable specific lints as needed. - Developer-friendly feedback
Provides clear, actionable messages that include code examples and links to documentation. This lowers the barrier to learning and fixing issues quickly. - Active maintenance and community support
Maintained under the Rust-lang umbrella with regular updates that keep pace with the evolution of the language. Contributions from the community help Clippy stay relevant and comprehensive. - CI/CD compatibility
Easily integrates into continuous integration pipelines to enforce linting standards consistently across all branches and contributors.
While Clippy is an essential tool for any Rust codebase, it has limitations that developers should understand, especially when building production-grade systems or working at scale.
- Focus on style over deep analysis
Clippy excels at enforcing style and catching straightforward mistakes but does not perform advanced semantic analysis. It cannot detect complex logical errors or concurrency issues that arise from nuanced ownership interactions across multiple modules. - No dedicated security scanning
Lacks targeted security analysis or integration with vulnerability databases. It does not detect dependency vulnerabilities or unsafe patterns beyond basic compiler warnings, requiring separate tools likecargo-auditfor full coverage. - No custom rule authoring
Clippy’s rules are built into the tool and cannot be extended by users. Teams with domain-specific standards or architectural rules cannot write custom lints to enforce their own guidelines. - Limited reporting options
Produces straightforward command-line output suited for developer consumption but lacks advanced reporting features such as structured machine-readable formats, dashboards, or issue tracking integration. - Single-language scope
Designed exclusively for Rust, Clippy does not support analysis of cross-language systems or projects where Rust components interface with other languages. This limits its effectiveness in polyglot architectures. - Scalability for large projects
On very large Rust codebases, Clippy can produce a high volume of warnings that require significant tuning to manage. Developers may need to invest time suppressing irrelevant lints or configuring the tool to reduce noise. - Minimal CI automation controls
While it can be added to CI pipelines, Clippy does not include advanced automation features like configurable fail thresholds for critical warnings, baselining, or suppression management across branches. - Limited contextual understanding
Clippy’s analysis is primarily syntactic and rule-based, lacking deep dataflow or control-flow analysis. It cannot trace issues that span multiple functions or modules in a way that more advanced static analysis tools can.
Clippy remains a highly effective and accessible tool for maintaining code quality in Rust projects. It offers immediate value by enforcing idiomatic practices and catching many classes of common errors early in development. However, for teams building complex, security-critical, or large-scale systems, Clippy is best used as part of a broader static analysis strategy that includes deeper semantic analysis, security scanning, and customizable enforcement capabilities.
rustc (Compiler Warnings)
The Rust compiler, rustc, is renowned for its clear, detailed, and actionable diagnostics. It is the first line of defense in ensuring code correctness and safety, providing compile-time checks that are central to Rust’s promise of memory safety without garbage collection. Unlike many languages where critical errors only surface at runtime, Rust’s compiler is designed to catch entire classes of bugs before code ever executes.
At its core, rustc offers more than just syntax validation. It performs deep semantic analysis, enforcing ownership rules, lifetimes, and type correctness, ensuring that developers write code free from data races, null pointer dereferences, and many other issues common in systems programming. Compiler warnings further enhance this by alerting developers to potentially problematic patterns that, while legal, may indicate logic errors or maintenance risks.
Key features include:
- Ownership and borrowing enforcement
Guarantees memory safety by enforcing strict rules on variable ownership, borrowing, and lifetimes at compile time. Prevents data races and dangling pointers without runtime overhead. - Rich type system checks
Validates types rigorously to prevent implicit casts and type errors, making APIs safer and more predictable. - Clear, user-friendly error messages
Offers detailed compiler messages with suggestions, code highlights, and actionable guidance that help developers fix issues quickly. - Compiler warnings for best practices
Alerts developers to dead code, unused variables, deprecated APIs, and other patterns that can lead to maintenance problems or bugs. - Continuous improvement and stability
Maintained as part of the official Rust project with frequent updates that evolve with the language. Benefits from the Rust team’s focus on stable, high-quality tooling. - Integration with cargo workflows
Works seamlessly with Rust’s package manager, makingcargo build,cargo check, andcargo teststandard parts of a developer’s workflow.
While rustc is one of the most advanced and helpful compilers available, relying solely on its warnings and errors for static analysis has limitations, especially for professional development teams with complex projects and security requirements.
Limitations in Issue Detection Scope
Unlike dedicated static analysis tools, rustc focuses primarily on correctness at the language level. It does not attempt to identify higher-level design issues, subtle logic bugs, or code smells that do not violate language rules. For example, it cannot detect inefficient algorithms, convoluted control flow, or violations of project-specific design patterns.
Absence of Style and Lint Enforcement Beyond Basics
rustc includes only a minimal set of built-in warnings about style and best practices. While it can warn about unused variables or deprecated APIs, it does not enforce a rich set of stylistic conventions or idiomatic usage. For teams wanting consistent formatting or adherence to idiomatic Rust patterns, tools like Clippy remain essential.
No Security Vulnerability Analysis
The compiler does not perform any security scanning for unsafe code blocks beyond basic unsafe warnings, nor does it analyze dependency vulnerabilities. It will not detect known CVEs in crates or flag potentially insecure code patterns like hardcoded secrets, leaving these concerns entirely to external tools.
Lack of Customizable Rules
rustc does not allow developers to define or enforce custom linting rules tailored to their organization’s needs. Teams cannot encode architectural guidelines, domain-specific invariants, or project-specific naming conventions directly in the compiler’s diagnostics.
Limited Reporting for Teams
Compiler output is designed for individual developers to use at their terminal or editor. It lacks advanced reporting features suitable for team workflows, such as structured JSON output for dashboards, historical trend tracking, or integration with issue trackers.
Minimal Integration with CI/CD Quality Gates
Although rustc errors will fail a build in CI by default, there is no built-in way to enforce specific warning levels or lint policies as blocking criteria. Teams have limited control over distinguishing between critical and minor issues in automated pipelines.
No Cross-Language or System-Level Analysis
rustc analyzes only Rust code. It does not understand or analyze interactions with code written in other languages that may be part of the same system. In projects with foreign function interfaces (FFI) or cross-language boundaries, this leaves a gap in static analysis coverage.
The Rust compiler’s rigorous checks are foundational to the safety and correctness guarantees that have made the language so popular. Its advanced error messages and compile-time enforcement of ownership rules prevent many classes of bugs outright. However, for organizations aiming for comprehensive code quality, security, and maintainability, rustc’s compiler warnings should be seen as a starting point, not the entire solution. Teams benefit most by combining the compiler’s checks with dedicated static analysis tools, linters, security scanners, and CI-integrated quality gates that cover a wider range of issues and provide richer insights.
cargo-audit
cargo-audit is a specialized security auditing tool for Rust projects, designed to help developers identify known vulnerabilities in their dependencies. It integrates tightly with Rust’s package management ecosystem and uses the RustSec Advisory Database to provide developers with actionable, up-to-date security information. By analyzing the Cargo.lock file, cargo-audit ensures teams are aware of public security advisories that could impact their software.
The tool is widely used in both open-source and professional contexts because it adds a crucial layer of security validation to Rust’s development workflow, which otherwise focuses primarily on correctness and safety at the language level.
Key features include:
- RustSec Advisory Database integration
Checks dependencies against a community-maintained database of security advisories for Rust crates. Ensures developers are aware of known vulnerabilities before deploying code. - Easy integration with cargo workflows
Runs via a simplecargo auditcommand, making it easy to add to local development routines. Compatible with standard Rust tooling without requiring significant configuration. - Detailed, actionable output
Reports include affected package versions, severity levels, CVE identifiers, and suggested remediation steps such as upgrading to a patched version. - CI/CD pipeline compatibility
Can be added to continuous integration systems to enforce security checks automatically on every build or deployment pipeline. - Support for yanked packages detection
Alerts developers when they depend on crates that have been yanked from crates.io, helping avoid unmaintained or problematic packages. - Active maintenance and community contributions
Backed by the RustSec project and widely adopted across the Rust ecosystem, ensuring it stays updated as new advisories are published.
While cargo-audit is an indispensable tool for security-conscious Rust teams, it has important limitations that users should consider to avoid relying on it as their only security safeguard.
Focused Scope on Known Vulnerabilities
cargo-audit only detects vulnerabilities that have been published in the RustSec Advisory Database. It cannot discover new or unknown security flaws in code or dependencies. If a crate contains a security bug that has not yet been disclosed, cargo-audit will not detect it, leaving teams potentially exposed.
No Static Code Analysis of Custom Code
The tool analyzes only dependency metadata in the Cargo.lock file. It does not review the project’s own source code for insecure patterns, unsafe usage, logic errors, or hardcoded secrets. For teams needing to validate the security of their own code, additional static analysis and manual review remain essential.
Limited Insight Into Transitive Dependencies Beyond Advisories
While cargo-audit can flag advisories in direct and transitive dependencies, it cannot analyze the actual code paths to determine whether vulnerable functionality is used. As a result, teams may see advisories even for vulnerabilities in unused code paths, requiring manual assessment to determine actual risk.
No Custom Rule Support or Organization-Specific Policies
cargo-audit cannot enforce internal security policies or coding guidelines. It offers no way to define custom security checks, organization-specific advisories, or rules for dependency selection beyond those present in the public advisory database.
Static Database Dependency and Update Needs
Effectiveness relies on regularly updating the local RustSec database copy. If teams fail to keep it up to date, they risk missing advisories. Although updates are straightforward, this maintenance step is critical for accurate results.
No Integration with Broader Vulnerability Management Systems
cargo-audit produces terminal-friendly output, which is excellent for developers but limited for integration into enterprise security systems. It lacks built-in support for sending structured data to vulnerability tracking tools, dashboards, or ticketing systems without additional scripting or customization.
Absence of License Compliance Checking
While essential for security auditing, cargo-audit does not analyze dependency licenses for compliance or policy violations. Teams with legal or compliance requirements need to use additional tools to validate licensing risks.
cargo-audit is a critical tool for managing supply chain security in Rust projects. By detecting known vulnerabilities in dependencies early in the development lifecycle, it enables teams to act proactively and reduce exposure to widely reported security flaws. However, its narrowly focused scope means that it should be used alongside other practices, including secure coding standards, code review, static analysis, and vulnerability management systems, to deliver comprehensive software security in production environments.
Rudra
Rudra is an advanced static analysis tool designed specifically to find memory safety issues in unsafe Rust code. Unlike most Rust analysis tools that focus on enforcing idiomatic style or known security advisories, Rudra performs deep static analysis to detect subtle, complex bugs that can arise when developers use Rust’s unsafe blocks to bypass compiler-enforced guarantees.
Developed originally by researchers at Facebook (now Meta), Rudra was created to address a critical gap in Rust’s ecosystem. While Rust’s ownership system ensures memory safety in safe code, unsafe code is still widely used in low-level libraries, FFI bindings, and performance-critical modules. Rudra’s purpose is to analyze such unsafe blocks rigorously to help maintain the same level of reliability that Rust is known for, even in contexts where compiler checks are intentionally circumvented.
Key features include:
- Static analysis of unsafe code blocks
Targets the most error-prone parts of Rust code where the compiler’s safety guarantees do not apply. Identifies potential memory safety vulnerabilities such as use-after-free, buffer overflows, and dangling pointers. - Soundness issue detection
Aims to find unsound APIs that can cause memory corruption or violate Rust’s type safety in downstream crates, even if their own unsafe usage seems valid in isolation. - Interprocedural analysis
Examines how unsafe operations propagate across function boundaries to catch vulnerabilities that simpler, intra-procedural tools might miss. - Focus on libraries and crates with unsafe code
Especially valuable for teams maintaining foundational crates that are widely reused in the ecosystem and need to guarantee safety even when using unsafe for performance or flexibility. - Research-driven design
Built on academic research, leveraging formal models of Rust’s semantics and common unsafe patterns to catch complex bugs. - Open source availability
Freely available to the Rust community, with the goal of improving the safety of widely used crates and raising the bar for the entire ecosystem.
Rudra is a highly specialized tool with impressive capabilities, but it also comes with important constraints that development teams should be aware of when considering it for their static analysis workflows.
Narrow Focus on Unsafe Rust Only
Rudra’s primary limitation is its scope. It analyzes unsafe blocks and is specifically designed to find memory safety bugs there. It does not analyze or lint safe Rust code for stylistic issues, logical errors, or general best practices. For projects that use little or no unsafe code, Rudra adds limited value.
High Complexity and Research-Prototype Nature
Rudra was designed as a research project, and while it is available as open source, it does not always offer the polished user experience or ease of integration that production-ready developer tools provide. Teams may face a learning curve to install, configure, and interpret its output effectively.
Limited CI/CD Integration Features
Unlike simpler linting tools or security scanners, Rudra does not come with built-in integrations for common CI/CD systems. Incorporating it into automated pipelines may require custom scripting and maintenance, which can be a barrier for teams without dedicated DevSecOps resources.
No General Security Vulnerability Scanning
Rudra does not check for known vulnerabilities in dependencies (like cargo-audit does) or flag unsafe use of outdated crates. It also does not scan for issues like hardcoded secrets, improper error handling, or API misuse unrelated to unsafe memory operations. Teams still need additional security tools to achieve comprehensive coverage.
Lack of Custom Rule Authoring
Rudra does not currently support defining custom checks or rules tailored to a specific project’s needs. It focuses on a curated set of analyses targeting known classes of unsafe memory safety bugs. For organizations wanting to enforce domain-specific guidelines or architectural policies, other tools will be needed.
Limited Reporting and Developer UX
Rudra’s output is designed for technical audiences familiar with Rust internals and unsafe code practices. Reports may be highly detailed but can be challenging to interpret for developers without deep knowledge of Rust’s safety model, requiring additional training or expertise.
Performance Considerations on Large Codebases
Because it performs interprocedural and semantic analysis, Rudra’s analysis can be computationally intensive. Running it on very large codebases may lead to long analysis times, making it less practical for frequent use in rapid development cycles without careful tuning.
Rudra is an essential tool for any Rust team that writes or depends on unsafe code. It helps bridge the gap between Rust’s strong safety guarantees and the flexibility unsafe code offers, ensuring that memory safety remains a priority even in the most performance-critical parts of a system. However, its specialized focus, integration challenges, and advanced output mean that it is best used as part of a broader static analysis and security strategy that includes linters, dependency scanners, and conventional code review practices.
MIRAI
MIRAI is an advanced static analysis tool for Rust designed to perform precise formal verification of program properties at compile time. It uses abstract interpretation to reason about possible program states, aiming to detect logic errors, contract violations, and potential security issues that can slip through traditional linting or compiler warnings.
Unlike tools focused purely on style or idiomatic usage, MIRAI targets semantic correctness. It analyzes Rust programs to check assertions, preconditions, postconditions, and invariants defined in code, enabling developers to catch deep logical bugs before deployment. MIRAI’s power lies in its ability to model complex program behavior, including branches, loops, and function calls, to ensure that critical properties hold in all possible executions.
Key features include:
- Formal verification of contracts
Allows developers to specify preconditions, postconditions, and invariants using Rust’spre,post, andassertmacros (via the contracts crate). MIRAI statically verifies that these conditions hold throughout the codebase. - Detection of logic errors
Identifies unreachable code, always-failing assertions, and infeasible branches, helping developers simplify and correct control flow. - Advanced symbolic execution
Uses abstract interpretation to explore multiple paths through code, detecting bugs that would not be found by simple syntactic analysis. - Support for analyzing complex Rust features
Handles common Rust constructs such as enums, pattern matching, generics, and ownership semantics, enabling practical analysis of real-world code. - Integration with Cargo
Provides a command-line interface that integrates with standard Rust development workflows, making it possible to analyze projects using familiar tooling. - Open source availability
Freely available to the Rust community with ongoing development and research backing.
MIRAI is a powerful tool that brings formal methods to practical Rust development, but it also has specific limitations and challenges that teams should consider carefully.
Narrow Focus on Contract-Based Verification
MIRAI excels at checking explicit contracts and assertions written by developers, but it will not automatically catch all types of bugs without these annotations. Its effectiveness depends on how thoroughly developers specify preconditions and invariants in their code. Without well-written contracts, MIRAI’s analysis will have limited coverage.
Steep Learning Curve and Expertise Requirements
Using MIRAI effectively requires familiarity with formal verification concepts, including writing precise contracts and interpreting counterexamples. For teams without prior experience in formal methods, onboarding can be challenging, potentially requiring training and process changes.
Integration and Usability Limitations
While MIRAI can be used via Cargo, its integration into developer workflows is less polished than simpler linting tools. It does not offer deep IDE integration or user-friendly GUIs out of the box, making it harder to adopt for teams accustomed to highly integrated developer experiences.
Performance Overhead on Large Codebases
MIRAI’s advanced analysis is computationally intensive. Analyzing large codebases with many functions and paths can lead to significant analysis times, which may limit its practicality for rapid iteration cycles or continuous integration runs without selective targeting.
Limited Detection of Non-Contract Issues
MIRAI does not replace tools like Clippy or cargo-audit. It will not enforce idiomatic style, catch dependency vulnerabilities, or identify unsafe code misuse unrelated to declared contracts. Its scope is specifically around verifying user-defined logical properties and invariants.
No Built-In Security Vulnerability Database Integration
Unlike cargo-audit, MIRAI does not check for known vulnerabilities in dependencies. While it can find logical bugs that might lead to security issues in code, it does not monitor for CVEs or yanked packages.
Limited Automation for Large Teams
MIRAI’s output is detailed and precise but not tailored for large-team workflows. It lacks built-in support for structured reporting formats, issue tracking integration, or dashboards that track contract violations over time, requiring teams to build additional tooling for full automation.
Dependency on User-Defined Contracts
Perhaps its biggest limitation is that MIRAI is only as good as the contracts developers write. Without consistent discipline in specifying correct and complete contracts, MIRAI’s ability to detect issues is reduced, making its value dependent on strong team practices.
MIRAI brings formal verification capabilities to Rust projects, offering a level of assurance that traditional static analysis tools cannot match. By rigorously verifying programmer-specified contracts, it helps eliminate entire classes of logic errors early in development. However, its specialized focus, learning requirements, and reliance on explicit annotations mean it is best seen as a complement to other analysis tools, forming part of a comprehensive quality and security strategy for professional Rust development teams.
Creusot
Creusot is an advanced formal verification framework for Rust that allows developers to specify and prove rich mathematical properties about their code. Unlike traditional static analysis or linting tools that catch style issues or common bugs, Creusot focuses on deep correctness guarantees through machine-checked proofs. It aims to bring formal methods typically found in academic or safety-critical software engineering into practical Rust development workflows.
Designed to work with a subset of Rust known as Creusot-Rust, the tool allows developers to annotate their code with specifications, such as preconditions, postconditions, invariants, and lemmas. Creusot then verifies these properties using automated theorem proving, ensuring that the implementation meets its formal specification.
Key features include:
- Formal specification support
Lets developers write precise preconditions, postconditions, invariants, and lemmas directly alongside Rust code. Supports rigorous documentation of expected behavior and constraints. - Machine-checked proofs
Uses SMT (Satisfiability Modulo Theories) solvers to automatically verify that code satisfies its specifications, providing strong guarantees of correctness that go beyond testing. - Integration with Rust syntax
Designed to feel natural to Rust programmers by working with idiomatic code. Creusot-Rust is a subset that maintains much of Rust’s familiar style while supporting formal reasoning. - Verification of functional correctness
Goes beyond detecting bugs by proving that code behaves exactly as specified. Ideal for critical algorithms, data structure invariants, and safety-critical logic. - Support for common Rust constructs
Handles enums, pattern matching, traits, generics, and other typical Rust features, making it applicable to realistic codebases rather than toy examples. - Open source and research-backed
Developed as an academic and community-driven project with the goal of improving software reliability through accessible formal verification.
While Creusot offers unique benefits for verifying Rust code, especially in critical systems, it also has notable constraints that development teams should evaluate carefully.
Specialized Focus on Formal Verification
Creusot is not designed to replace general-purpose linters, security scanners, or dependency auditors. Its scope is verifying that user-specified properties hold. Without writing these formal specifications, Creusot cannot analyze or prove much about the code, leaving large parts of a project unchecked if not thoroughly annotated.
Learning Curve for Formal Methods
Using Creusot effectively requires understanding formal verification principles, writing clear specifications, and interpreting proof results. Teams unfamiliar with formal methods may need training and practice to use it productively, which can slow adoption.
Restricted to a Rust Subset
Creusot works with Creusot-Rust, which is a constrained subset of the full Rust language. Certain advanced Rust features may not be fully supported or may require rewriting code to fit within Creusot’s verification model. This can limit its applicability for large, complex, or highly idiomatic Rust codebases.
No Analysis of Unsafe Blocks
Creusot is focused on verifying safe Rust code. It does not analyze or verify the correctness of unsafe blocks where the compiler’s guarantees are explicitly bypassed. For projects that rely heavily on unsafe code for performance or FFI, this creates verification gaps.
Lack of Security Vulnerability Database Checks
Creusot does not check for known security issues in dependencies like cargo-audit does. It also does not analyze for common security patterns such as hardcoded secrets, improper error handling, or unsafe API usage outside its formal specification context.
Limited CI/CD Integration Features
Although Creusot can be run as part of a build process, it lacks polished integration features for CI/CD systems. Teams may need to develop custom scripts and workflows to enforce verification checks automatically in pipelines.
No Custom Linting or Stylistic Rules
Creusot is not a linting tool and offers no mechanism to enforce style guides, naming conventions, or idiomatic usage. Teams still need to use Clippy or other linters to maintain consistent coding standards.
Performance Considerations
Formal verification is computationally intensive. Running Creusot on large codebases or very complex functions can lead to long verification times, which may not be suitable for rapid development cycles without selective application.
Creusot is a powerful tool for Rust teams that need to prove critical correctness properties with mathematical rigor. By enabling developers to write and verify formal specifications, it offers a level of assurance that goes beyond testing and traditional static analysis. However, its focus on formal verification, learning requirements, subset language constraints, and integration challenges mean that it is best viewed as a specialized addition to a broader toolkit for maintaining software quality, rather than a standalone solution for all code analysis needs.
Prusti
Prusti is a static verifier for Rust programs that brings formal verification techniques into everyday development workflows. Built on top of the Rust compiler, Prusti allows developers to write formal specifications such as preconditions, postconditions, and invariants directly in Rust code using contracts. It then uses automated reasoning to verify these specifications, helping ensure that code behaves correctly in all possible executions.
Unlike typical static analysis tools that focus on style or common bug patterns, Prusti targets deep logical correctness. It is designed to catch subtle bugs that might only appear under specific conditions and to provide machine-checked guarantees that certain errors are impossible. By integrating closely with Rust’s ownership and type systems, Prusti enhances the language’s safety model with user-defined behavioral contracts.
Key features include:
- Formal contracts in Rust
Supports writing preconditions, postconditions, loop invariants, and assertions using Rust-style annotations. These contracts describe expected behavior and constraints explicitly in the code. - Automated verification
Uses an SMT (Satisfiability Modulo Theories) solver to check that the code satisfies its contracts across all possible execution paths, eliminating entire classes of logical bugs. - Close integration with Rust compiler
Works with standard Rust tooling and leverages the compiler’s existing type and borrow checking to make verification practical for real-world Rust projects. - Support for common Rust constructs
Handles pattern matching, enums, traits, generics, and other typical Rust features, making it more usable on realistic codebases than many academic verification tools. - Detailed counterexample reporting
When verification fails, Prusti provides concrete counterexamples to help developers understand exactly why a contract was violated. - Open source and research-backed
Developed as part of academic research to bring formal verification into mainstream Rust development, with an active community and ongoing improvements.
While Prusti offers advanced capabilities for ensuring correctness, it also has specific limitations that teams should carefully consider before adopting it.
Reliance on User-Defined Contracts
Prusti’s effectiveness depends entirely on the quality and coverage of the contracts developers write. Without clear and thorough specifications, Prusti cannot verify much about a codebase. This means developers must invest time in understanding and writing precise contracts to benefit from the tool.
Limited Support for Unsafe Rust
Prusti is designed for verifying safe Rust code. It does not analyze or verify correctness in unsafe blocks, where the compiler’s guarantees are relaxed. For projects that use unsafe code for performance or FFI, this leaves potential gaps in verification coverage.
Language Subset and Feature Limitations
Prusti does not yet support all of Rust’s features. Certain advanced constructs, such as complex macros or highly dynamic patterns, may be unsupported or require simplification to be verifiable. This can limit its applicability in large, mature codebases that use Rust’s full feature set.
Steep Learning Curve for Teams
Effectively using Prusti requires developers to learn formal verification concepts, such as writing contracts and interpreting counterexamples. Teams without prior experience in formal methods may face a significant learning curve to adopt Prusti productively.
Performance and Scalability Challenges
Formal verification is computationally demanding. Analyzing large functions with complex control flow or verifying large codebases can lead to long analysis times. This makes running Prusti on every commit or in rapid CI cycles challenging without careful scoping.
Minimal IDE and CI/CD Integration
Prusti’s integration into developer workflows is still evolving. It does not yet have deep IDE integration for in-editor contract writing and verification feedback, and adding it to CI/CD pipelines often requires custom scripting.
No Security Vulnerability Database Integration
Unlike tools like cargo-audit, Prusti does not check for known vulnerabilities in dependencies. Its focus is strictly on verifying functional correctness of user-written code, not on supply chain security or dependency risk.
Lack of General Linting and Style Checks
Prusti does not enforce stylistic conventions or idiomatic Rust patterns. Teams still need to use tools like Clippy to maintain consistent style and best practices alongside Prusti’s formal verification.
Prusti brings rigorous formal verification to Rust development, enabling developers to prove that their code behaves exactly as intended under all conditions. It is especially valuable for critical algorithms, data structures, and safety-sensitive logic. However, its reliance on explicit contracts, learning requirements, language subset constraints, and limited automation support mean it is best used as a complement to traditional static analysis, linters, security scanners, and thorough code review practices to achieve comprehensive code quality and safety.
Kani
Kani is a formal verification tool purpose-built for analyzing Rust programs at the level of the LLVM intermediate representation (IR). Developed and maintained by AWS, Kani aims to make formal verification of Rust code practical and scalable by performing bounded model checking (BMC). This approach systematically explores all possible program states up to a user-specified bound to prove or refute properties about the code.
Kani is particularly well-suited to safety-critical systems, embedded software, cryptographic libraries, and other contexts where developers want high confidence that their Rust code is free from certain classes of bugs. By modeling all feasible execution paths within specified bounds, Kani can detect subtle logical errors that are difficult to uncover with testing or conventional static analysis.
Key features include:
- Bounded model checking
Systematically analyzes all possible execution paths up to a given bound to ensure correctness properties hold under all scenarios within those limits. - Support for Rust assertions
Verifies standard Rustassertstatements, ensuring that developer-defined safety and correctness conditions always hold within the chosen bounds. - Harness-based verification model
Lets developers write verification harnesses, which are specialized entry points used to describe the conditions and inputs Kani should verify, offering fine-grained control over analysis scope. - Memory safety verification
Proves absence of memory safety errors such as buffer overflows, null dereferences, or use-after-free within the specified bounds, even for code with unsafe blocks. - Support for unsafe Rust
Unlike many tools that ignore unsafe code, Kani analyzes it explicitly, helping ensure safety properties even in performance-critical or systems-level code. - Integration with Cargo
Works seamlessly with the standard Rust tooling, making it easy for Rust developers to incorporate verification into their existing workflows with minimal friction. - Detailed counterexample generation
When verification fails, Kani provides concrete counterexamples showing exactly how a property can be violated, greatly aiding debugging and remediation. - Open source with AWS support
Actively developed with backing from AWS, ensuring ongoing improvements, documentation, and community engagement.
While Kani brings powerful formal verification capabilities to Rust development, there are important considerations and trade-offs teams should understand before adopting it.
Analysis Bound Limitations
Kani’s model checking is bounded, meaning its guarantees hold only within the specified execution bounds (e.g., loop unroll limits, recursion depth). Properties that depend on unbounded behavior or extremely deep state spaces may go unchecked unless specifically scoped and tuned. This introduces the risk of false negatives if the bounds are set too low.
Requires Writing Verification Harnesses
Kani’s effectiveness depends on well-written verification harnesses that define the conditions and inputs to explore. Without thoughtful harness design, important paths may be missed. Teams must invest time and expertise to write meaningful harnesses that capture real-world usage scenarios.
Performance and Scalability Considerations
Bounded model checking is computationally intensive. As code complexity grows, the number of states Kani must explore increases exponentially, which can lead to long analysis times or even make verification intractable without adjusting bounds or refactoring code.
Limited IDE Integration and Developer UX
Kani’s primary interface is command-line-based and oriented toward build automation. While clear and precise, its output is not yet deeply integrated into popular Rust IDEs or editors, making it less accessible for day-to-day incremental development feedback.
Not a General-Purpose Linter or Style Checker
Kani is focused on proving correctness properties. It does not enforce Rust style guidelines, idiomatic usage, or typical lint rules. Developers still need tools like Clippy to maintain consistent coding standards and idiomatic practices.
No Dependency Vulnerability Checking
Unlike cargo-audit, Kani does not analyze dependencies for known security advisories or supply chain risks. It cannot warn developers if a dependency contains a CVE or has been yanked from crates.io.
Requires Formal Thinking and Expertise
Effectively using Kani often requires developers to think formally about their code, design precise harnesses, and interpret counterexamples. Teams without experience in formal verification may face a learning curve to adopt it productively.
Output and Reporting Focused on Experts
While Kani’s error reporting is detailed, it is tailored toward users comfortable with formal methods and low-level program analysis. Developers unfamiliar with model checking concepts may need additional training to make full use of the tool’s insights.
Kani brings state-of-the-art formal verification capabilities to Rust, particularly for systems-level and safety-critical development where memory safety and correctness are non-negotiable. By systematically proving properties of Rust code, including unsafe blocks, it helps teams eliminate entire classes of bugs that might escape testing. However, its bounded nature, performance costs, harness requirements, and learning curve mean that it is best seen as a specialized addition to a broader suite of development and analysis tools that together ensure the quality, security, and maintainability of Rust software.
Seer
Seer is an experimental static analysis tool designed to detect subtle, correctness-critical bugs in Rust programs using symbolic execution techniques. Developed by researchers at Purdue University, Seer targets a unique space in the Rust tooling ecosystem by aiming to identify logical errors that can arise even in safe Rust code, which typically benefits from the language’s strong compile-time guarantees.
Unlike linters or style checkers, Seer focuses on semantic issues. It systematically explores program paths symbolically to detect logical flaws such as assertion failures, invalid inputs that break preconditions, and control-flow mistakes that might escape both compiler checks and traditional testing. By analyzing Rust code in a path-sensitive manner, Seer is able to find bugs that would only manifest under specific, hard-to-test conditions.
Key features include:
- Symbolic execution for Rust
Analyzes program paths by representing inputs as symbolic values, enabling the exploration of a vast space of possible executions without manual test input generation. - Assertion violation detection
Identifies code paths that can causeassertstatements or contract conditions to fail, helping developers eliminate logic errors that would otherwise slip through to production. - Automatic input generation for bug discovery
Produces concrete input examples that trigger assertion failures, making it easier for developers to reproduce and understand bugs. - Focus on safe Rust analysis
Unlike many static analyzers that focus exclusively on unsafe code, Seer is designed to find subtle semantic errors in fully safe Rust codebases. - Research-grade precision
Built on academic research to deliver precise, path-sensitive bug detection that complements Rust’s type and borrow checking systems. - Open source and community-accessible
Freely available to the Rust community for experimentation and improvement, with ongoing research backing its development.
While Seer offers unique capabilities for uncovering deep correctness issues in Rust code, it also comes with practical and conceptual limitations that teams should consider when evaluating its use in real-world projects.
Limited Maturity and Production Readiness
Seer remains a research-oriented, experimental tool rather than a mature, production-ready solution. It may not offer the stability, ease of use, or polished integration that professional teams expect from critical development tools. Installing, configuring, and maintaining Seer can require effort and familiarity with research prototypes.
Narrow Focus on Assertion Violations
Seer’s primary strength is detecting code paths that can violate explicit assertions or preconditions. It does not serve as a general-purpose linter or style checker and will not enforce idiomatic usage, naming conventions, or common Rust best practices that tools like Clippy handle.
No Dependency Vulnerability Analysis
Unlike tools such as cargo-audit, Seer does not examine a project’s Cargo.toml or Cargo.lock files to identify known security vulnerabilities in dependencies. It offers no supply chain security coverage, leaving this critical concern to other tools in the ecosystem.
No Analysis of Unsafe Code Blocks
Seer’s design is focused on safe Rust code, leaving unsafe blocks largely outside its analysis scope. For projects that include unsafe code for performance or FFI, Seer does not provide the memory safety verification or advanced checking found in tools like Kani or Rudra.
Performance and Scalability Constraints
Symbolic execution is inherently computationally intensive. As code complexity grows, the number of feasible paths explodes, leading to long analysis times or resource exhaustion. For large projects or highly dynamic code, this can limit Seer’s practicality without selective analysis or careful path pruning.
Lack of Custom Rule Authoring
Seer does not provide a framework for defining custom rules or checks tailored to specific project or organization standards. Its detection capabilities are centered on assertions and control-flow correctness, limiting flexibility for broader static analysis needs.
Minimal IDE and CI/CD Integration
Seer is primarily a command-line tool with research-grade output. It lacks robust integrations with popular Rust IDEs, editors, or CI/CD systems. Teams adopting it will likely need to develop custom scripts and processes to incorporate Seer into their workflows meaningfully.
Learning Curve for Symbolic Execution Concepts
Effectively using Seer requires an understanding of symbolic execution, constraint solving, and counterexample interpretation. Developers unfamiliar with these formal methods may face a learning curve to apply Seer’s insights productively.
Seer brings advanced research techniques to Rust static analysis, offering a powerful way to uncover deep, path-sensitive bugs that evade traditional testing and compiler checks. It is particularly well-suited to safety-critical logic where even subtle assertion failures are unacceptable. However, its experimental nature, narrow focus on assertion violations, lack of unsafe code analysis, and limited integration features mean it is best viewed as a specialized, complementary tool for teams with the expertise and resources to leverage its capabilities alongside other Rust static analysis, linting, and security tools.
Flowistry
Flowistry is a sophisticated static analysis and visualization tool for Rust that focuses on understanding dataflow in Rust programs. Built as a Rust analyzer extension and command-line tool, Flowistry helps developers see how data moves through their code, making ownership, borrowing, and mutation patterns transparent in a way that is often hard to grasp just from reading source code.
Designed to address one of Rust’s most unique features—the ownership system—Flowistry is especially valuable for helping developers write safer, clearer, and more maintainable code. It serves both as a learning aid for those new to Rust’s borrowing semantics and as a practical debugging and review tool for experienced developers working on complex projects with intricate lifetimes and ownership flows.
Key features include:
- Precise dataflow analysis
Performs static analysis to track how data is moved, borrowed, mutated, or dropped across functions and modules. - Visual ownership insights
Provides clear visualizations that show which variables are mutated or borrowed at specific program points, helping to explain compiler errors and ownership conflicts. - IDE integration
Works with popular Rust development environments like Visual Studio Code via rust-analyzer, allowing in-editor visualization of dataflow and ownership. - Command-line interface
Supports terminal-based workflows for analysis and inspection outside of IDEs, making it flexible for different development styles. - Support for common Rust idioms
Handles enums, pattern matching, traits, and other typical Rust features in its analysis, making it applicable to real-world codebases. - Educational use cases
Particularly valuable for teaching Rust’s ownership model, as it makes invisible compiler checks and rules explicit and easier to understand. - Open source and community-maintained
Freely available for developers to use and extend, with ongoing contributions from the Rust community to improve capabilities and usability.
While Flowistry offers unique and valuable insights into Rust’s ownership system, it also has distinct limitations that teams should consider when deciding how to use it in practice.
Focus on Understanding Rather Than Enforcing Rules
Flowistry’s primary goal is to explain ownership and borrowing, not to enforce coding standards or check for correctness errors. It does not flag bugs, enforce lints, or guarantee that code follows best practices. Instead, it helps developers understand why code does or doesn’t compile, which is invaluable for learning but less direct for quality enforcement.
No Detection of Logic Bugs or Security Issues
Flowistry is not designed to catch logical errors, assertion failures, or security vulnerabilities. Unlike static analyzers that check for correctness properties or dependency issues, Flowistry will not identify dangerous logic mistakes or known CVEs in dependencies. Teams need other tools like cargo-audit or formal verifiers for these concerns.
No Analysis of Unsafe Code Semantics
While Flowistry models ownership in safe Rust code very well, it does not offer semantic verification of unsafe blocks. For projects that use unsafe Rust, it will not help understand potential memory safety violations introduced by manual pointer manipulation or unchecked operations.
Limited Integration with CI/CD Pipelines
Flowistry is designed as a developer aid rather than an automated gatekeeper. It does not integrate natively with continuous integration systems to enforce policies or block builds. Its value lies in manual exploration and visualization during development.
Not a Linting Tool
Flowistry does not enforce style guidelines, naming conventions, or idiomatic usage like Clippy does. It cannot flag overly complex expressions, anti-patterns, or violations of team code style policies. Teams will still need separate linters to maintain style consistency.
Performance on Large Codebases
While Flowistry can handle realistic Rust projects, its static analysis can become slower or less manageable on very large codebases with deeply nested ownership chains. Interactive use in such contexts may require patience or selective analysis of specific modules.
Learning Curve for Effective Use
Although Flowistry is designed to make Rust’s ownership system clearer, it still requires developers to understand the basics of ownership, borrowing, and lifetimes to interpret its visualizations effectively. Developers entirely new to Rust may need to pair Flowistry with tutorials or training to get full benefit.
Flowistry fills a unique role in the Rust tooling ecosystem by demystifying one of the language’s most powerful but challenging features. By making ownership and borrowing relationships explicit and visual, it empowers developers to write safer, clearer code and to debug confusing borrow checker errors more efficiently. However, its role is best seen as complementary: Flowistry helps developers understand Rust’s model, while other static analysis, linting, and security tools help enforce correctness, security, and maintainability across entire codebases.
Polonius
Polonius is an advanced borrow checker engine developed as part of the Rust compiler project to improve the precision, maintainability, and future extensibility of Rust’s ownership and borrowing analysis. Named after a character in Shakespeare’s Hamlet, Polonius represents a more formal, declarative approach to borrow checking compared to Rust’s original implementation.
At its core, Polonius aims to solve limitations of the current borrow checker by making analyses more precise and sound, especially in the context of non-lexical lifetimes (NLL). While Rust’s standard borrow checker already enables safe memory management without a garbage collector, it can be conservative in certain scenarios, rejecting code that is actually safe. Polonius introduces a more detailed, data-driven analysis that can accept more valid Rust programs while preserving Rust’s strong safety guarantees.
Polonius is implemented in Rust’s compiler as an optional, experimental engine. It is not a standalone user-facing static analysis tool but rather an internal component with a formalized model that is easier to reason about, verify, and eventually extend.
Key features include:
- Declarative borrow checking
Uses a declarative Datalog-based model to represent borrow checking rules, making the logic clearer and easier to validate formally. - Support for non-lexical lifetimes
Precisely handles Rust’s NLL system, which allows borrows to end before the end of a lexical scope, reducing false positives and enabling more flexible borrowing patterns. - Improved analysis precision
Accepts more valid programs by accurately modeling the flow of references and borrows, avoiding unnecessary rejections seen in the classic borrow checker. - Formal specification
Designed with a clear, formalized set of rules that make it easier for researchers and compiler engineers to reason about borrow checking soundness. - Integration with the Rust compiler
Implemented as an experimental engine in rustc, available on nightly builds for testing and research. Developers can experiment with it to understand potential future improvements to Rust’s default borrow checking. - Long-term maintainability
Engineered to make the borrow checker’s implementation more maintainable and extensible for future Rust evolution, such as supporting more advanced ownership patterns.
While Polonius represents a significant advance in Rust’s borrow checking research and design, it is important to understand its specific role and the limits of what it provides.
Not a Standalone Developer Tool
Polonius is not designed for direct use by developers as a command-line tool or IDE extension. Unlike linters, static analyzers, or formal verifiers, it is an internal engine that runs as part of the compiler. Developers cannot install or run Polonius separately to analyze their code outside of the compiler.
Experimental and Not Yet Default
As of today, Polonius is considered experimental and is not the default borrow checker in stable Rust. Developers can opt into using it on nightly builds, but it is not guaranteed to be stable or fully optimized for all production workloads.
Focused Solely on Borrow Checking
Polonius addresses borrow checking only. It does not perform other kinds of static analysis such as linting for idiomatic usage, security scanning for dependency vulnerabilities, or formal verification of functional correctness. Other tools are needed to cover these dimensions of code quality.
No Detection of Logic Bugs or Security Flaws
While Polonius improves the precision of borrow checking, it does not detect general logic errors, assertion failures, or security issues unrelated to ownership and lifetimes. Developers still need testing, reviews, and static analysis tools like Clippy, MIRAI, or cargo-audit for comprehensive safety.
No Support for Unsafe Code Verification
Polonius models Rust’s safe borrowing rules but does not analyze the semantics of unsafe blocks, where developers bypass the borrow checker intentionally. Bugs in unsafe code remain the developer’s responsibility and are outside Polonius’s analysis scope.
Limited Developer Visibility and Reporting
Because it is a compiler-internal component, Polonius does not produce specialized reports, dashboards, or structured output for developer consumption. Its benefits appear indirectly by accepting more valid code or rejecting unsound code more precisely.
Performance Considerations in Large Codebases
While designed with precision in mind, Polonius’s data-driven model introduces performance challenges. As of now, it can be slower than the classic borrow checker on large projects, which is one reason it remains experimental.
Polonius represents Rust’s commitment to advancing its core safety guarantees through formal, precise, and maintainable analysis of ownership and borrowing. It is a critical investment in the language’s long-term usability and soundness, particularly for supporting more flexible and expressive borrowing patterns without sacrificing safety. However, for developers today, Polonius is best understood as a behind-the-scenes improvement to the compiler rather than a general-purpose static analysis tool. Teams should continue using the existing Rust compiler, Clippy, security scanners, and formal verification tools to ensure comprehensive quality and safety in Rust projects while watching Polonius’s evolution as part of Rust’s future.
Miri
Miri is an interpreter for Rust’s mid-level intermediate representation (MIR) that enables precise, step-by-step execution of Rust programs to catch undefined behavior at compile time. Unlike conventional testing or static analysis tools, Miri runs Rust code in an environment that simulates execution while enforcing the strictest rules of Rust’s memory model. This allows it to detect subtle and often dangerous bugs that might pass unnoticed during typical development or even at runtime in certain cases.
Included in the Rust toolchain as a cargo subcommand (cargo miri), Miri is especially valued for verifying that unsafe code adheres to Rust’s aliasing and memory safety rules. It is also capable of checking for correctness in safe code, particularly in complex cases where the compiler’s static analysis cannot prove safety on its own.
Key features include:
- Execution of MIR with safety checks
Interprets Rust code at the MIR level while enforcing Rust’s memory safety guarantees, catching errors such as use-after-free, unaligned memory access, or invalid pointer dereferences. - Detection of undefined behavior
Flags undefined behavior in unsafe code, helping ensure that even manually managed memory operations adhere to Rust’s guarantees. - Supports safe and unsafe Rust
Checks both safe and unsafe code paths, making it a powerful tool for validating libraries that rely on unsafe blocks for performance or FFI. - Integration with cargo
Usable viacargo miri, enabling straightforward inclusion in Rust workflows without complex setup. - Detailed error reporting
Provides precise diagnostic output, indicating exactly where and why undefined behavior occurs. - Assists in developing safe abstractions
Essential for library authors who implement safe APIs on top of unsafe code, ensuring that their abstractions do not hide unsound behavior. - Experimental support for foreign function interfaces (FFI)
While limited, Miri can simulate some interactions with C libraries, helping validate mixed-language code where safety boundaries can be subtle. - Open source and actively maintained
Part of the Rust project, with ongoing improvements and integration into the wider Rust toolchain.
Despite its valuable capabilities, Miri has important limitations and trade-offs that developers should understand when adopting it in their workflow.
Not a Replacement for Traditional Testing
Miri does not generate tests or validate correctness in terms of expected outputs. It focuses on detecting undefined behavior rather than asserting that algorithms compute correct results. Developers still need unit tests, integration tests, and property-based tests to verify logical correctness.
Limited Support for Dynamic Features and System Calls
Miri cannot fully emulate all system-level operations. Code that relies on OS-specific features, I/O, networking, or threading primitives may fail or be unsupported in Miri’s environment. As a result, developers may need to write special harnesses or isolate code sections to analyze them effectively.
Slower Than Native Execution
Because Miri interprets code rather than compiling it to native instructions, it is significantly slower than normal execution. Analyzing large codebases or running complex computations with Miri can be time-consuming, limiting its practicality for large-scale automated checking.
No Analysis of Dependency Vulnerabilities
Miri does not scan for known vulnerabilities in dependencies, unlike tools like cargo-audit. It cannot warn about outdated crates with security advisories, so supply chain security requires separate tooling.
Does Not Enforce Style or Idiomatic Usage
Miri is not a linter and does not care about code style, naming conventions, or idiomatic Rust usage. Developers still need Clippy and other style-focused tools to maintain consistent and idiomatic code.
Focused on Memory Safety, Not General Logic Bugs
While Miri is excellent at detecting undefined behavior, it does not identify general logic errors such as off-by-one mistakes in safe code, incorrect algorithms, or violation of domain-specific invariants. These require other forms of testing or formal verification.
Experimental FFI Support Limitations
Miri’s ability to interpret foreign function calls is limited and experimental. Complex FFI scenarios or highly platform-specific C code may not be fully analyzable with Miri, requiring separate review and testing strategies.
Learning Curve for Effective Use
Although Miri’s basic usage is simple via cargo miri, effectively interpreting its output and structuring code for analysis can be non-trivial, especially in projects with complex ownership patterns or advanced unsafe code. Developers may need to invest time to understand how best to use Miri in their context.
Miri is a powerful addition to Rust’s suite of correctness tools, providing a unique way to catch undefined behavior that is invisible to the compiler and hard to reproduce with traditional testing. By simulating execution with strict safety checks, it helps ensure that both safe and unsafe code adhere to Rust’s rigorous guarantees. However, it is best seen as a complement to other tools—used alongside linters, static analyzers, security scanners, and thorough testing to deliver comprehensive confidence in Rust codebases.
cargo-scan
cargo-scan is a security-focused static analysis tool designed to help Rust developers detect vulnerabilities and insecure patterns in their codebases. Unlike dependency scanners like cargo-audit that focus on known advisories in external crates, cargo-scan analyzes your project’s actual Rust source code, flagging potential security issues before they make it into production.
Built on the Semgrep engine, cargo-scan leverages rule-based pattern matching to identify insecure coding patterns, anti-patterns, and common mistakes that can lead to vulnerabilities. It is designed to integrate seamlessly into Rust development workflows, providing developers with a lightweight but practical way to introduce security scanning directly into their CI/CD pipelines and local development.
Key features include:
- Static code security scanning
Analyzes your Rust source code for potential vulnerabilities, such as hardcoded secrets, insecure API usage, or unsafe cryptographic practices. - Semgrep-based engine
Uses Semgrep’s flexible pattern-matching engine under the hood, enabling advanced rule definitions and precise detection of security issues. - Curated rule sets
Includes a set of pre-built rules tailored for common Rust security pitfalls, helping developers catch issues even without deep security expertise. - Custom rule support
Allows teams to define their own security rules to enforce organization-specific guidelines or policies. - Cargo integration
Works with Cargo commands (cargo scan), making it easy to run scans in the same workflows developers already use. - CI/CD pipeline compatibility
Can be integrated into continuous integration systems to automatically scan pull requests and new commits for security issues before merging. - Readable, actionable reports
Produces human-friendly output with clear explanations of detected issues and guidance on remediation. - Open source and actively maintained
Freely available to the Rust community, with ongoing improvements and updates to rule sets and detection capabilities.
While cargo-scan provides valuable security scanning capabilities for Rust projects, there are important limitations and trade-offs to be aware of when adopting it.
Rule-Based Detection Limits
cargo-scan relies on pattern matching rather than deep semantic or formal analysis. It can only detect issues that match its defined rules. This means it may miss subtle, context-dependent security vulnerabilities or novel attack patterns not covered by existing rules.
Potential for False Positives
Like other static analyzers using pattern-based rules, cargo-scan may produce false positives—flagging code that is actually safe but matches a suspicious pattern. Developers need to review results carefully and tune rules to balance sensitivity and noise.
Limited Support for Unsafe Code Analysis
cargo-scan does not perform deep verification of unsafe blocks in the way that tools like Rudra or Miri do. While it can flag certain unsafe usages via patterns, it lacks the semantic understanding needed to prove or refute memory safety in complex unsafe code.
No Analysis of Dependency Vulnerabilities
cargo-scan focuses on scanning your own project’s source code. It does not analyze the Cargo.lock file for known vulnerabilities in external crates like cargo-audit does. For full supply chain security, teams must use cargo-audit in parallel.
No Formal Verification Capabilities
cargo-scan does not attempt to prove the correctness of code against formal specifications or contracts. Tools like Prusti or MIRAI remain necessary for verifying precise functional properties and invariants.
Limited IDE Integration
While cargo-scan works well in terminal and CI environments, it does not offer deep integration with popular Rust IDEs or editors for inline scanning and feedback during development.
Performance on Large Codebases
Scanning very large projects can be slower, especially if using many custom rules or very broad patterns. Developers may need to scope scans or optimize rules to maintain practical performance in CI pipelines.
Requires Security Expertise for Custom Rules
While cargo-scan supports custom rule authoring, writing effective and precise security rules typically requires security knowledge. Teams lacking this expertise may find it harder to maximize the value of custom rule sets without support or training.
cargo-scan is a valuable addition to the Rust security toolkit, helping teams identify and remediate insecure coding patterns in their own projects before they ship. It complements other tools focused on dependency scanning, memory safety, and formal verification, delivering practical, accessible static security analysis that fits naturally into modern development and CI/CD workflows. By combining cargo-scan with other security-focused practices, Rust teams can build stronger, safer software while maintaining the productivity and ergonomics Rust is known for.
Rust Language Server (RLS)
Rust Language Server (RLS) is a development tool that provides real-time, editor-integrated support for the Rust programming language. It implements the Language Server Protocol (LSP), enabling popular IDEs and editors to offer rich, context-aware features like code completion, go-to definition, and inline error checking for Rust code.
RLS is designed to improve developer productivity and code quality by making Rust’s powerful compiler diagnostics, syntax checking, and refactoring tools available directly in the developer’s editor. By providing an always-on analysis experience, RLS reduces the feedback loop between writing code and catching mistakes, helping developers adopt Rust’s best practices and maintain high-quality codebases.
Key features include:
- Real-time error and warning reporting
Surfaces compiler errors and warnings directly in the editor as code is written, helping catch mistakes early. - Code completion
Offers intelligent autocompletion based on types, traits, methods, and module contents to speed up development and reduce typos. - Go-to definition and find references
Lets developers jump directly to symbol definitions and discover where items are used across the codebase. - Hover documentation
Displays inline documentation for types, functions, and traits, making it easier to understand APIs without leaving the editor. - Symbol search and navigation
Enables fast searching of functions, structs, traits, and other symbols in large projects. - Formatting support
Integrates with rustfmt to enforce consistent code style across teams automatically. - Integration with popular editors
Supports editors like Visual Studio Code, Sublime Text, Atom, and more via the LSP. - Uses rustc’s analysis
Leverages the actual Rust compiler to deliver accurate, idiomatic feedback that aligns with Rust’s strict safety guarantees. - Open source and maintained by the Rust project
Developed by the Rust community and supported by official tooling efforts, ensuring alignment with Rust’s evolving language features.
While RLS dramatically improves the developer experience for Rust projects, there are important considerations and limitations to understand when deciding how to use it effectively.
Focus on Developer Experience, Not Analysis Enforcement
RLS is primarily designed to aid development by surfacing errors and offering productivity features. It does not enforce linting rules, style conventions, or security policies automatically in CI/CD pipelines. Teams still need tools like Clippy or cargo-audit to enforce policy and check for security vulnerabilities in production workflows.
Limited Static Analysis Beyond Compiler Errors
RLS surfaces compiler diagnostics, but it does not perform advanced static analysis like detecting logical errors, dataflow problems, or memory safety issues in unsafe code. For deeper analysis, tools like Clippy, Rudra, or MIRAI remain necessary.
No Formal Verification or Proof Capabilities
RLS does not support writing or verifying formal specifications, preconditions, or postconditions in the way tools like Prusti or Creusot do. It cannot prove functional correctness or invariants beyond what the compiler enforces.
No Security Vulnerability Scanning
RLS does not check for known security vulnerabilities in dependencies. Unlike cargo-audit, it does not analyze Cargo.lock files for advisories or monitor the supply chain for outdated or vulnerable crates.
Performance Considerations on Large Codebases
RLS can consume significant memory and CPU resources when indexing and analyzing large projects, sometimes causing sluggish editor performance. For very large monorepos or highly modular projects, developers may need to tune settings or accept reduced responsiveness.
Limited Support for Some Advanced Language Features
Because RLS builds on Rust’s compiler internals, it occasionally lags behind the latest Rust nightly features or experimental syntax. Developers using cutting-edge language features may encounter reduced support or need to fall back to alternative tools like rust-analyzer.
Migration to rust-analyzer
The Rust project has announced that rust-analyzer is the next-generation replacement for RLS, offering better performance, richer features, and improved long-term maintainability. While RLS remains usable and maintained, many teams are encouraged to adopt rust-analyzer for future-proof development.
Rust Language Server (RLS) has been a foundational tool for bringing first-class IDE support to Rust, lowering the learning curve and making the language more accessible to newcomers and productive for professionals. By integrating compiler-powered feedback directly into editors, RLS improves code quality during development. However, it is best seen as part of a broader toolkit that includes linters, security scanners, formal verification tools, and CI/CD automation to deliver comprehensive quality and safety in Rust projects.
Crafting Robust, Secure, and Maintainable Rust Projects
Ensuring quality, security, and maintainability in Rust projects requires much more than relying on the compiler alone. Rust’s safety guarantees are industry-leading, but they work best as part of a layered approach that combines multiple analysis, verification, and productivity tools. Each tool we explored targets different but complementary goals in the software development lifecycle, offering teams a holistic strategy for building robust Rust systems.
At the foundation are tools like rustc (Compiler Warnings) and Clippy, which enforce correctness, idiomatic style, and best practices right in the developer workflow. They reduce basic errors early and maintain consistent code quality across teams.
For security, cargo-audit and cargo-scan play vital roles. cargo-audit protects against known supply chain vulnerabilities by checking dependencies for published advisories, while cargo-scan focuses on your own source code, finding insecure patterns before they ship. These tools make sure that the code you write and the libraries you depend on remain secure.
Advanced static analysis and formal verification tools, including MIRAI, Prusti, Creusot, Kani, Seer, and Rudra, address deeper correctness and safety challenges. They help catch subtle logic errors, prove critical invariants, or verify memory safety even in unsafe blocks. For projects with high-assurance requirements or safety-critical components, these tools are essential to eliminate entire classes of bugs that runtime testing might miss.
Miri offers a unique approach by interpreting Rust code to detect undefined behavior at compile time, especially valuable when working with unsafe code. Polonius, as an experimental borrow checker engine, improves the compiler’s precision and is laying the groundwork for more expressive but safe patterns in Rust’s future.
Supporting the developer experience, Rust Language Server (RLS) and Flowistry make Rust’s advanced semantics more accessible. RLS provides real-time error checking, code navigation, and productivity features in IDEs, while Flowistry visualizes ownership and dataflow to demystify Rust’s borrowing model.
Together, these tools enable Rust teams to address every layer of code quality:
- Correctness and idiomatic usage with compiler checks and linting
- Security with dependency scanning and static code analysis
- Formal verification of critical properties and invariants
- Memory safety assurance even in unsafe code
- Improved developer workflows with integrated, real-time feedback and visualization
No single tool can deliver everything. The real strength comes from combining them into a tailored workflow that matches your team’s needs, project complexity, and risk profile. By thoughtfully integrating these tools into development, review, and CI/CD pipelines, Rust teams can achieve their main goals: writing reliable, secure, maintainable code that delivers on Rust’s promise of safety and performance without compromise.


