
What Happens When You Skip Chaos Testing in APM Planning
IN-COM December 23, 2025 Compliance, Impact Analysis, Information Technology, Tech TalkApplication Performance Monitoring strategies are often designed around steady state assumptions that rarely hold under real failure conditions. Dashboards, thresholds,...
Read More
Detecting COBOL Code Vulnerable to Log Poisoning
IN-COM December 15, 2025 Applications, COBOL Posts, Compliance, Data Management, Tech TalkEnterprise COBOL systems rely heavily on logs as authoritative records of execution behavior, transaction outcomes, and exception handling paths. In...
Read More
Developer Productivity Tools and Platforms for Large Codebases and Portfolio Complexity
IN-COM December 13, 2025 Compliance, Data, Information Technology, Tech Talk, Tools and SolutionsDeveloper productivity in enterprise environments is no longer defined by individual coding speed or tool familiarity. It is shaped by...
Read More
Enterprise IT Risk Management: From Risk Identification To Continuous Control
IN-COM December 12, 2025 IT Risk Management, Application Modernization, Compliance, Legacy SystemsInformation technology risk management has evolved from a supporting governance function into a core discipline shaping enterprise resilience, regulatory posture,...
Read More
Essential Refactoring Techniques to Cut Maintenance Costs
IN-COM December 9, 2025 Code Review, Compliance, Impact Analysis, Tech TalkRefactoring has become a decisive lever for reducing maintenance spending as enterprise systems accumulate structural complexity that elevates operational effort....
Read More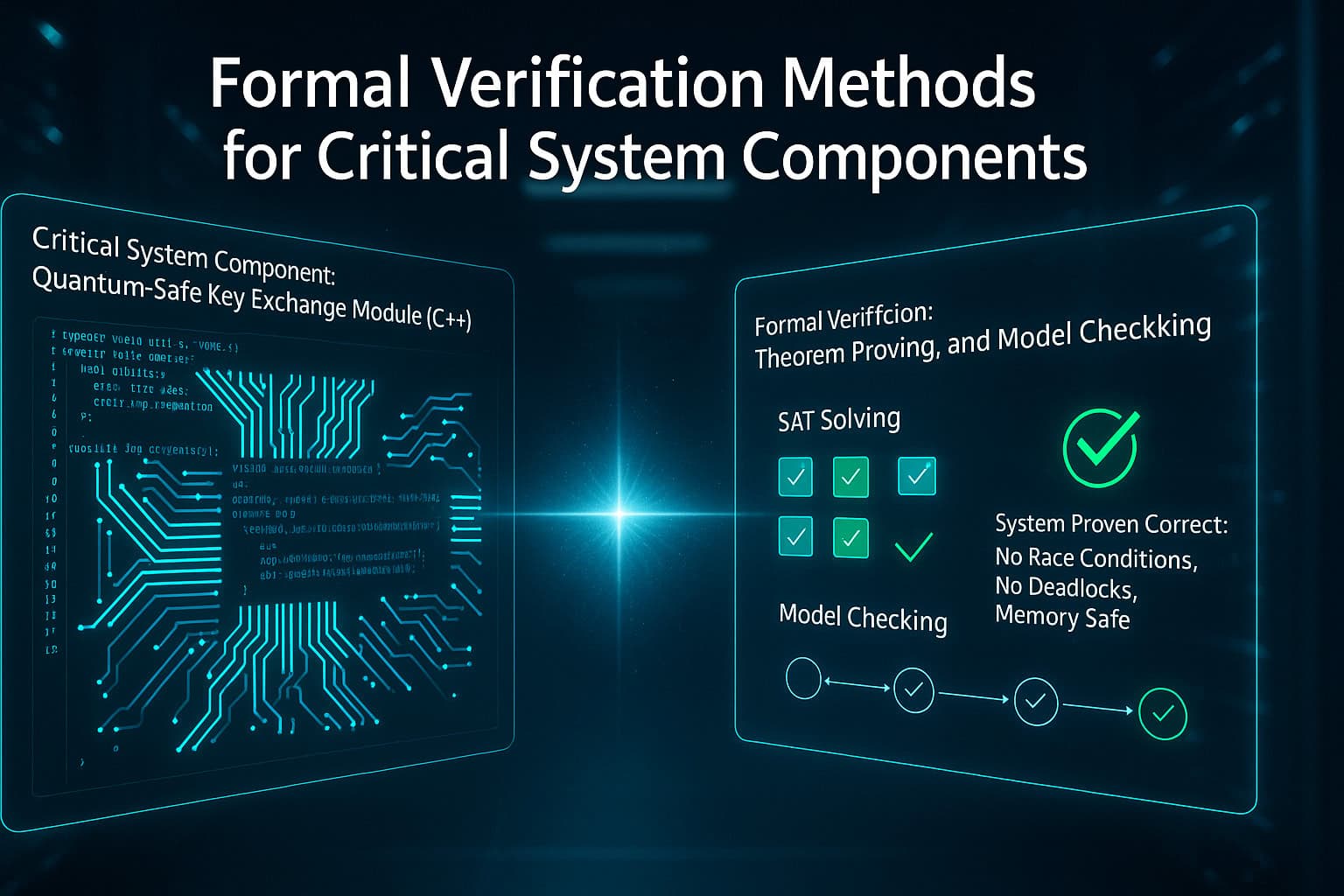
Formal Verification Methods for Critical System Components
IN-COM December 8, 2025 Applications, Code Review, Compliance, Data Modernization, Legacy Systems, Tech TalkFormal verification has become a defining capability for organizations responsible for operating safety critical and mission dependent systems. Modernization initiatives...
Read More
