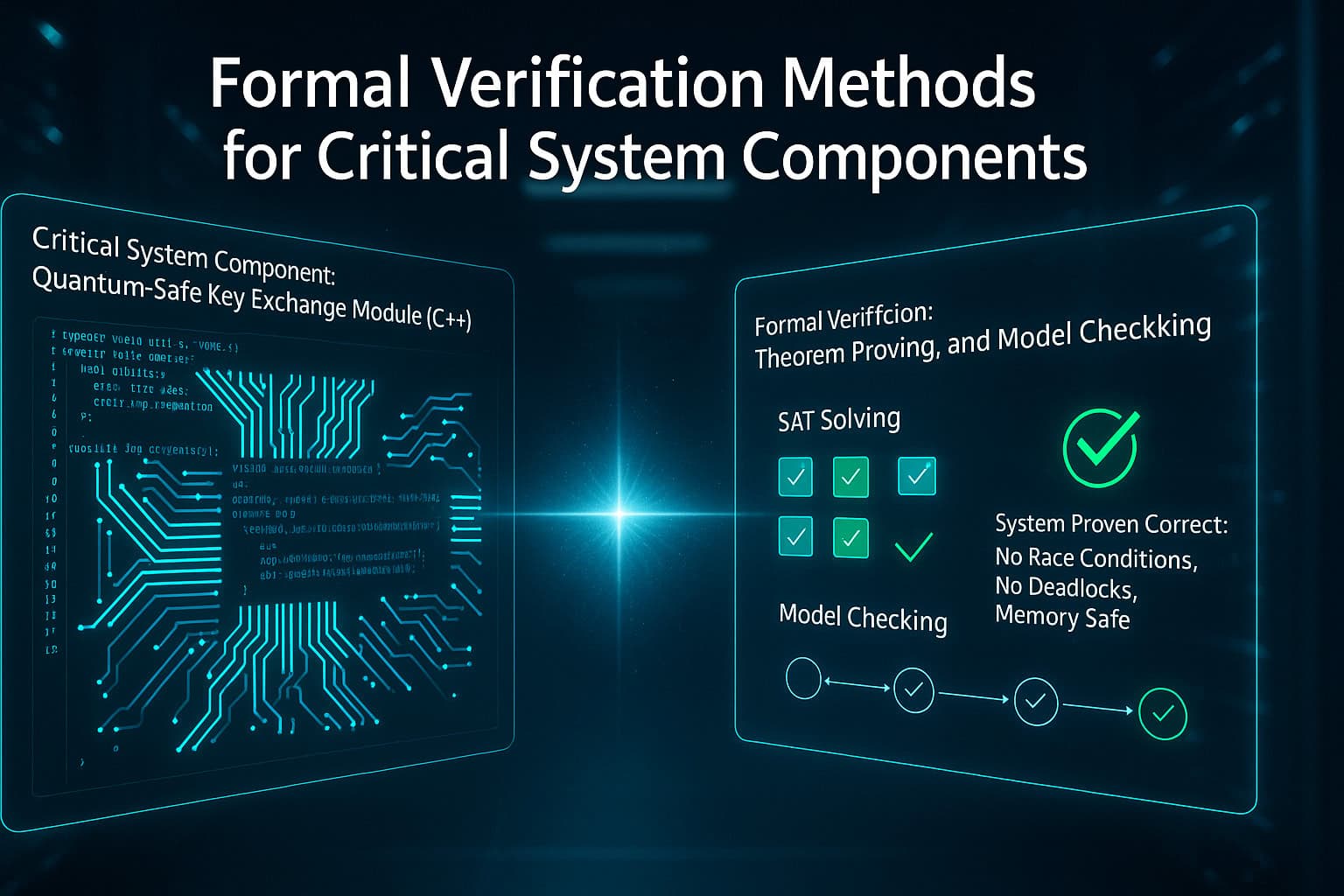
Formal Verification Methods for Critical System Components
IN-COM December 8, 2025 Applications, Code Review, Compliance, Data Modernization, Legacy Systems, Tech TalkFormal verification has become a defining capability for organizations responsible for operating safety critical and mission dependent systems. Modernization initiatives...
Read More
Leveraging Machine Learning to Detect Architectural Violations Before Refactoring
IN-COM December 6, 2025 Artificial Intelligence (AI), Compliance, Impact Analysis, IT Risk ManagementArchitectural violations accumulate gradually in large enterprise systems as modules evolve under competing constraints, shifting ownership boundaries and extended maintenance...
Read More
Taint Analysis for Tracking User Input Through Complex, Multi-Tier Applications
IN-COM December 6, 2025 Compliance, Data Modernization, Impact Analysis, Legacy SystemsTaint analysis has become an essential capability for enterprises operating complex, multi tier applications where user supplied data passes through...
Read More
Using AI to Calculate the Risk Score of Every Legacy Code Module
IN-COM December 5, 2025 Applications, Artificial Intelligence (AI), Compliance, Impact Analysis, Tech TalkEnterprise modernization programs increasingly require a defensible and repeatable method for evaluating technical risk across sprawling legacy estates. As systems...
Read More
Best Practices for Quantum-Safe Cryptography Migration Planning
IN-COM December 4, 2025 Artificial Intelligence (AI), Compliance, Data, Tech TalkEnterprise leaders are preparing for a cryptographic transition that will reshape security architectures across mainframe estates, distributed ecosystems, and cloud...
Read More
What Percentage of Legacy Code Can Realistically Be Refactored by AI?
IN-COM December 3, 2025 Artificial Intelligence (AI), Compliance, Data, Impact Analysis, Legacy SystemsAI driven refactoring has become an influential component in enterprise modernization programs, yet the proportion of legacy code that can...
Read More
